(在家觀看 = 0%,在校觀看 = 100%)
100% 在校觀看日期及時間:
自由選擇,點選以下地區觀看辦公時間及位置
課時: 162 小時
(84 小時課堂 + 78 小時於家中透過上網來控制本中心的器材及軟件,並依照筆記來進行實習)
享用時期: 42 星期。進度由您控制,可快可慢。
課堂錄影導師:Franco
在校免費試睇:首 3 小時,請致電以上地點與本中心職員預約。
半費重考。開始觀看最後 1 堂之 1 個月內為保障期限。請務必向本中心購買考試券。
本課程提供在校免費重睇及導師解答服務。
(在家觀看 = 100%,在校觀看 = 0%)
100% 在家觀看日期及時間:
每天 24 小時全天候不限次數地觀看
課時: 162 小時
(84 小時課堂 + 78 小時於家中透過上網來控制本中心的器材及軟件,並依照筆記來進行實習)
享用時期: 42 星期。進度由您控制,可快可慢。
課堂錄影導師:Franco
在校免費試睇:首 3 小時,請致電以上地點與本中心職員預約。
半費重考。開始觀看最後 1 堂之 1 個月內為保障期限。請務必向本中心購買考試券。
本課程提供導師解答服務。
Cisco Systems Inc. 是全球最大的網路設備生產商,在世界各地設有 120 個以上的分支據點。Cisco 的產品包括 Switch (交換器)、LAN Router (區域網路由器)、WAN Router (廣域網路由器)、IOS (Internetwork Operating System) 網路管理操作系統、ASA (Adaptive Security Appliances)、IPS (Intrusion Prevention System)、ISE (Identity Services Engine)、WSA (Web Security Appliance)、ESA (Email Security Appliance) 等。全球的大企業、銀行、大學和政府機構之網路設備,無一不採用 Cisco 的產品,管理 Cisco 網路設備便成為一門專業的學問。為了能證明你有專業水準來安裝、設定及管理 Cisco 的網路安全產品,Cisco 便推出其 CCNP Security (Cisco Certified Network Professional - Security,Cisco 認可網路安全專業人士) 國際認可考試。要考取 CCNP Security 國際認可證書,必須通過以下 4 科的考試及持有有效的 CCNA Security 證書:
- CCNP Security: SENSS (Implementing Cisco Edge Network Security Solutions)
- CCNP Security: SIMOS (Implementing Cisco Secure Mobility Solutions)
- CCNP Security: SISAS (Implementing Cisco Secure Access Solutions)
- CCNP Security: SITCS (Implementing Cisco Threat Control Solutions)
CCNP Security 能大大提升你的安裝、管理及解救網路安全產品的水平,並能令你處理大型網路安全環境,而下列為 CCNP Security 能給你的部份好處:
- 令你將只有 CCNA 證書的對手比下去,令你更易求職、升職或競爭到生意。
- 令你於跨國企業、電訊機構或互聯網供應商的電腦部門成為高級資訊安全技術顧問。
- 令你於中、小企業的電腦部門成為管理階層,由你來規劃網路,然後指派只有 CCNA 證書的下屬來實踐你的規劃。
- 絕對能滿足你對網路安全技術的求知慾,因會有很多你一知半解或甚至從未聽過的知識給你學懂,大大增長你的網路安全技術知識。
- 只要透徹理解了CCNP Security 的知識及充份掌握了 CCNP Security 的實習,日後要考取全電腦界公認為最頂級的證書 CCIE : Security (Cisco Certified Internetwork Expert : Security),便只是一步之差!
本中心的 CCNP Security 國際認可證書課程由 Franco Tsang (擁有 CCIE : Security, CCIE : Service Provider 及 CCIE : Routing and Switching 三項 CCIE 證書) 籌備多時,精心編排。由上堂、溫習、實習、考試研習、做試題至最後考試,均為你度身訂造,作出有系統的編排。務求真正教識你,又令你考試及格。
本課程緊貼時代需要,相關的概念 / 內容 / 產品能被應用到不同的情景中,例如:
- 在 AWS 上玩 Cisco ASA (Adaptive Security Appliance) 9.9:
https://www.facebook.com/systematic.hk/photos/a.173134451964/10155191936036965/ - SSL / TLS 評分由 A+ (滿分, without CAA) 到 A+ (滿分, with CAA):
https://www.facebook.com/systematic.hk/photos/a.173134451964/10155639668736965/ - RSA 效能測試:
https://www.facebook.com/systematic.hk/photos/a.173134451964/10154270184056965/ - MAC Flap + 收到過千萬個的 broadcasts + CPU% 超高:
https://www.facebook.com/systematic.hk/photos/a.173134451964/10153938556931965/ - 更多應用情景 / 導師在 Facebook 所分享的文章:
https://www.systematic.com.hk/course_Franco.htm?panel=2
| 課程名稱: |
CCNP Security 國際認可證書課程 - 簡稱:CCNP Security Training Course |
| 課程時數: | 合共 162 小時 課堂 84 小時 (共 28 堂) 及實習時段 78 小時 (共 26 節) |
| 適合人士: | 具備 CCNA Security 知識的人士 |
| 授課語言: | 以廣東話為主,輔以英語 |
| 課程筆記: | 本中心導師親自編寫英文為主筆記,而部份英文字附有中文對照。 |
CCNP Security (Cisco 認可網路安全專業人士) 其實是由 Cisco 頒發的一項國際認可高級證書。高級證書意即你不能直接考取 CCNP Security,而必須首先考取到 Cisco 的初級證書 CCNA Security (Cisco 認可網路安全夥伴),才可考取 CCNP Security。 |
| 考試編號 | 科目名稱 | 簡稱 | 考試費 |
| 300-206 | Implementing Cisco Edge Network Security Solutions | SENSS | HK$2,348 (需另加 2.5% 行政費) |
| 300-209 | Implementing Cisco Secure Mobility Solutions | SIMOS | HK$2,348 (需另加 2.5% 行政費) |
| 300-208 | Implementing Cisco Secure Access Solutions | SISAS | HK$2,348 (需另加 2.5% 行政費) |
| 300-210 | Implementing Cisco Threat Control Solutions | SITCS v1.5 | HK$2,348 (需另加 2.5% 行政費) |
本中心為 Cisco 指定的 CCNP Security 國際認可考試試場,報考時請致電本中心,登記欲報考之科目考試編號、考試日期及時間 (最快可即日報考)。 臨考試前要繳付考試費 (見上表),及必須出示下列兩項有效之身份證明文件,否則考生不可進行考試,而已繳付之考試費亦不會退回: 考試題目由澳洲考試中心傳送到你要應考的電腦,考試時以電腦作答。所有考試題目均為英文,而大多數的考試題目為單項選擇題 (意即 O) 或多項選擇題 (意即 口),其餘則為配對題及實戰題。作答完成後會立即出現你的分數,結果即考即知!考試不合格便可重新報考,不限次數。欲知道作答時間、題目總數、合格分數等詳細考試資料,可瀏覽本中心網頁 "各科考試分數資料"。 |
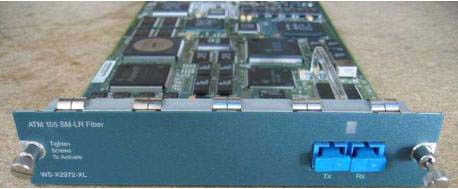
為進一步加強本中心 Cisco 的課程質素,本中心投放大量資源購買 Cisco 器材,以供學員進行實習。以下是本中心擁有的 Cisco 器材 (種類繁多,未能盡錄): |
 |
 |
| Cisco Router 800 Series (ISR) | Cisco Router 2500 Series |
 |
 |
| Cisco Router 2600 Series | Cisco Router 2800 Series (ISR) |
 |
 |
| Cisco Router 2900 Series (ISR) | Cisco Router 3600 Series |
 |
 |
| Cisco Router 3800 Series (ISR) | Cisco Router 4000 Series |
 |
 |
| Cisco Catalyst Switch 1900 Series | Cisco Catalyst Switch 2950 Series |
 |
 |
| Cisco Catalyst Multilayer Switch 3550 Series | Cisco Catalyst Multilayer Switch 3560 Series |
 |
 |
Cisco Catalyst Multilayer Switch 3560X Series |
Cisco Catalyst Multilayer Switch 3750G Series |
 |
 |
| Cisco Catalyst Multilayer Switch 3750X Series | Cisco Catalyst Multilayer Switch 5000 Series |
 |
 |
| Cisco PIX Firewall | Cisco LightStream 1010 ATM Switch |
 |
 |
| Cisco ATM Module | Cisco FXS Voice Module |
 |
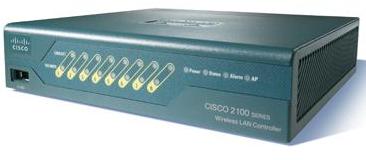 |
| Cisco IP Phone 7911G | Cisco Wireless LAN Controller 2106 |
 |
 |
| Cisco Aironet Lightweight Access Point 1130AG | PSTN Simulator |
 |
 |
| ISDN Simulator | Cisco ASA 5505 |
 |
 |
| Cisco ASA 5510 | Cisco ASA 5512X |
 |
|
| Cisco IPS 4210 |
|
課程名稱:CCNP Security 國際認可證書課程 - 簡稱:CCNP Security Training Course |
SENSS
1 Layer 2 security
1.1 Ethernet frame structure
1.1.1 Ethertype
1.2 Security in MAC address table
1.2.1 Common attacks in MAC address table
1.2.1.1 Preventing MAC Address Table Attacks
1.2.1.2 Lab: Advanced port security: Study the characteristics of sticky mac address on trunk links.
1.3 VLAN Security
1.3.1 Basic VLAN concept
1.3.2 Basic Trunk concept
1.3.3 DTP (Dynamic Trunking Protocol)
1.3.4 Trunking protocols
1.3.5 Tagging Attack - VLAN Hopping
1.3.5.1 802.1Q or ISL Tagging Attack or Information Gathering
1.3.5.2 Double-Encapsulated 802.1Q
1.3.6 Private VLAN
1.3.6.1 Protected Switchport
1.3.6.2 Lab: Protected Switchport
1.3.6.3 Private VLAN
1.3.6.4 Lab: Private VLAN (Isolated)
1.4 DHCP Security issues
1.4.1 DHCP Process
1.4.2 Attacks Against DHCP
1.4.2.1 Countermeasures to DHCP Exhaustion Attack (DHCP starvation attack)
1.4.2.2 Countermeasures to Rouge DHCP Server
1.4.2.3 Lab: DHCP Snooping
1.4.2.4 DHCP Snooping Binding Table
1.4.3 Protecting ARP Infrastructure
1.4.3.1 Basic ARP Review
1.4.3.2 ARP spoofing attack
1.4.3.3 Dynamic ARP Inspection (DAI)
1.4.3.4 Lab: Dynamic ARP Inspection
1.4.3.5 Lab: Dynamic ARP Inspection with ARP ACL
1.4.4 Miscellaneous topics about DHCP security issues
1.4.4.1 IP Source Guard
1.4.4.2 Lab: IP Source Guard
1.5 Traffic Storm Control (Traffic Suppression)
1.5.1.1 Lab: Traffic Storm Control
1.6 MACSec
1.6.1 Switch-to-host (Downlink MACsec)
1.6.2 Switch-to-switch (Uplink MACSec)
2 IOS Zone-Based Firewall / IOS FW
2.1 Introduction of IOS Zone Based Firewall
2.1.1 Cisco Policy Language (CPL) Configuration
2.1.1.1 Define zones
2.1.1.2 Define zone-pairs
2.1.1.3 Define class-maps
2.1.1.4 Define policy-maps
2.1.2 Lab: Basic Zone Based Firewall
2.1.3 Lab: Advanced Zone-Based Firewall Configuration
2.2 Regular Expression and its application in traffic filtering
2.2.1 Lab: Filtering web traffic to franco.com
3 Cisco ASA (Cisco Adaptive Security Appliance) features
3.1 Introduction to ASA
3.1.1 Common ASA Models
3.1.2 Modules used in ASA
3.1.2.1 ASA AIP-SSM
3.1.2.2 Gigabit Ethernet Extension Modules
3.1.3 ASA Base and Security+ (Security Plus) license
3.2 Cisco ASA 1000V
3.2.1 Introduction to Cisco ASA 1000V
3.2.2 VSG Network Deployment Design
3.2.3 Installation of Cisco ASA 1000V
3.2.4 Apply Cisco ASA 1000V license
3.3 Cisco ASA Initialization
3.3.1 Configuration File Management
3.3.2 Configure ASA Interfaces
3.3.2.1 Security Level Overview
3.3.2.2 Lab: Configure hostname in Cisco ASA.
3.3.2.3 Lab: Configure “inside” interface with static IP address 10.0.0.15 /8
3.3.2.4 Lab: Configure “outside” interface with DHCP client feature
3.3.2.5 Configure Basic IPv6 on the ASA
3.3.2.6 Lab: Configure “outside” interface with PPPoE client feature.
3.3.2.7 ASA DHCP Server
3.3.2.8 Lab: Study the meaning of security-level
3.3.3 ASA Management Access Configuration
3.3.3.1 Enable Password
3.3.3.2 Lab: Configure Enable password
3.3.3.3 Telnet Access
3.3.3.4 Lab: Configure telnet access in ASA - part 1
3.3.3.5 Lab: Configure telnet access in ASA - part 2
3.3.3.6 SSH (Secure Shell) Access
3.3.3.7 Lab: Configure SSH Access in ASA
3.3.3.8 ASDM (Adaptive Security Device Manager)
3.3.3.9 Lab: Configure ASDM
3.4 Network management in ASA
3.4.1 Lab: NTP
3.4.2 System message severity levels
3.4.2.1 Lab: Enable and configure general properties of system logging
3.4.2.2 Lab: Enable console logging
3.4.2.3 Lab: Terminal logging
3.4.2.4 Lab: Logging to syslog servers
3.4.2.5 Lab: ASDM logging
3.4.2.6 Lab: Buffer logging
3.4.2.7 Lab: Buffer logging: manual flash logging
3.4.2.8 Lab: Buffer logging: automatic flash logging
3.4.2.9 Lab: Buffer logging – automatic save log to FTP
3.4.2.10 Logging list
3.5 Network Access Control
3.5.1 Access list types
3.5.2 Access control entry order
3.5.3 Extended access list
3.5.3.1 Lab: Basic extended access list
3.5.3.2 Lab: Add an ACE to an existing extended access list
3.5.4 Standard access list
3.5.4.1 Lab: An example of using standard ACL in ASA – Part 1
3.5.4.2 Lab: An example of using standard ACL in ASA – Part 2
3.5.5 IPv6 access list
3.5.5.1 Lab: IPv6 access list
3.5.6 Advanced access control list topics
3.5.6.1 Object grouping
3.5.6.2 Object grouping: protocols
3.5.6.3 Object grouping: networks
3.5.6.4 Object grouping: services
3.5.6.5 Object grouping: ICMP Types
3.5.6.6 Object-Group nesting
3.5.6.7 Lab: ACL with object grouping
3.5.6.8 Time-based ACL
3.5.6.9 Lab: Time-Base ACL
3.5.6.10 ICMP filtering
3.5.6.11 Lab: configure ICMP Access in ASA
3.6 Application layer filtering
3.6.1 Basic content filtering
3.6.1.1 Lab: Filter Java in ASA
3.6.2 URL Filtering
3.7 Modular Policy Framework
3.7.1 Features provided by Modular Policy Framework
3.7.2 Default Modular Policy Framework
3.7.3 Default Inspection: DNS
3.7.4 Default Inspection: FTP
3.7.5 Default Inspection: ESMTP and SMTP
3.7.6 Default Inspection: TFTP
3.7.7 Default Inspection: H.323
3.7.8 Lab: Layer 3 / 4 Inspection
3.7.9 Inspection Policy-Map
3.7.10 Deep Inspection (HTTP and FTP)
3.7.10.1 Lab: HTTP Inspection - Blocking specific request method
3.7.10.2 Lab: HTTP Inspection – Block specific URL
3.7.10.3 Lab: HTTP Inspection - Block specific browser
3.7.10.4 Lab: HTTP Inspection – Block specific content type
3.7.10.5 Lab: HTTP Inspection – Block specific content
3.7.10.6 Lab: FTP Deep Inspection - Block FTP commands
3.8 NAT (Network Address Translation)
3.8.1 Basic NAT concepts
3.8.2 Dynamic NAT concepts
3.8.3 Dynamic NAT with overload concepts
3.8.4 Static NAT concepts
3.8.5 Lab: Configure Static NAT
3.8.6 Lab: Static NAT with PAT
3.8.7 Lab: Dynamic NAT with overload
3.8.8 Lab: Dynamic NAT with public ip pool
3.8.9 Lab: Dynamic NAT with public ip pool with interface ip address for last resort
3.8.10 Advanced NAT Topics – Twice NAT
3.8.10.1 Lab: Twice NAT (Part 1)
3.8.10.2 Lab: Twice NAT (Part 2)
3.8.10.3 Lab: Twice NAT (Part 3)
3.8.11 Advanced NAT Topics – DNS and NAT
3.8.11.1 Lab: NAT with DNS (Part 1)
3.8.11.2 Lab: NAT with DNS (Part 2)
3.9 ASDM (Adaptive Security Device Manager)
3.9.1 Lab: Topology build up
3.9.2 Lab: ASDM: Configure hostname
3.9.3 Lab: ASDM: Configure interfaces
3.9.4 Lab: ASDM: Configure static default gateway
3.9.5 Lab: ASDM: Configure NTP
3.9.6 Lab: ASDM: Configure IP extended access-list
3.9.7 Lab: ASDM: Dynamic NAT (Port Address Translation)
3.9.8 Lab: ASDM: Static NAT (Port Redirection)
3.9.9 Lab: ASDM: HTTP inspection
3.10 Traffic monitoring
3.10.1 Capture
3.10.1.1 Lab: Capture all traffic in the outside interface
3.10.2 “show conn”
3.10.2.1 Lab: Monitor the connection by “show conn”
3.10.3 Packet-tracer
3.10.3.1 Lab: Trace a packet by “packet-tracer”
3.11 Transparent mode
3.11.1 Routed mode
3.11.2 Transparent mode
3.11.2.1 Lab: Configure transparent mode firewall
3.11.3 Ethertype access list
3.11.3.1 Lab: EtherType access list
3.11.4 ARP inspection
3.11.4.1 Lab: ARP inspection
3.12 SNMPv3
3.12.1 Basic SNMP
3.12.2 SNMPv3 security models and levels
3.12.3 Lab: SNMPv3 in ASA through command line interface
3.12.4 Lab: SNMPv3 in ASA through ASDM
3.13 Scanning threat detection
3.13.1 Botnet Traffic Filter
3.13.1.1 Dynamic database / static database
3.13.1.2 DNS snooping
3.13.1.3 Classification
3.14 Multiple Contexts
3.14.1 Basic concept of Multiple Contexts
3.14.2 Moment to use Multiple Contexts
3.14.3 Limitations of Multiple Contexts
3.14.4 Configuration Logics in Multiple Contexts
3.14.5 Admin Context
3.14.6 Classifiers
3.14.7 Demonstration: Change from single mode to multiple mode
3.14.8 Demonstration: Create contexts, create and assign interfaces to contexts
3.14.9 Demonstration: Configure admin context
3.14.10 Demonstration: Configure custom context franco1
3.14.11 Demonstration: Configure custom context franco2
3.15 Failover
3.15.1 Introduction to Failover
3.15.2 Hardware requirements
3.15.3 Software requirements
3.15.4 Failover link
3.15.5 Failover Behaviour
3.15.6 Demonstration: Failover
4 Advanced SSH Topics
4.1 SCP (Secure copy)
4.1.1 Lab: SCP (Secure copy)
4.2 Passwordless SSH with public keys and private keys
4.2.1 Lab: Passwordless SSH with public keys and private keys
5 Security Management
5.1 Cisco Prime Infrastructure
5.2 Cisco Security Manager (CSM)
5.2.1 Local policies and shared policies
6 Device hardening
6.1 Hardening techniques in Cisco IOS routers and firewall
6.2 Hardening techniques in Switches
7 Appendix – Physical topology
SIMOS
1 IPSec VPN with IKEv1 in IOS
1.1 IPSec Standards
1.2 Types of IPSec VPNs
1.2.1 Site-to-Site VPN
1.2.2 Tunnel Building Process for Site-to-Site IPSec VPN
1.2.3 Remote-Access VPN
1.2.4 Tunnel Building Process for Remote-Access IPSec VPN
1.3 Details concepts of IKE Phase 1
1.3.1 Management Connection
1.3.1.1 Main Mode
1.3.1.2 Aggressive Mode
1.3.2 Diffie-Hellman
1.3.3 Peer Authentication
1.3.4 Configuring IKE Phase1
1.3.4.1 Configuring IKE Policy
1.3.4.2 Options available in an IKE Policy
1.3.5 Lab: Configure IKE Policy
1.3.6 Configure IKE peer authentication
1.3.6.1 Lab: Configure IKE Pre-Shared Key
1.3.6.2 Lab: Configure IKE RSA Encryption Nounce
1.3.7 IOS Certificate Authority
1.3.7.1 Lab: Part 1 of 2: Configure IOS CA
1.3.7.2 Lab: Part 2 of 2: Configure Router1 to obtain certificate from IOS CA
1.4 Details concepts of IKE Phase 2
1.4.1 Crypto Access List
1.4.2 Transform Set
1.4.3 Crypto Map
1.4.3.1 Static Crypto Map and Dynamic Crypto Map
1.5 Site-to-Site (L2L) VPN
1.5.1 Lab : Site-to-Site (L2L) VPN
1.5.2 CACCTP (Crypto Access Check on Clear-Text Packet)
1.5.2.1 Lab: CACCTP (Crypto Access Check on Clear-Text Packet)
1.5.3 Dynamic Crypto Map
1.5.3.1 Lab: Site-to-Site (L2L) VPN with dynamic crypto map
1.5.4 Advanced topics in Dynamic Crypto Map – TED (Tunnel Endpoint Discovery)
1.5.4.1 Lab: TED (Tunnel Endpoint Discovery)
1.5.5 GRE over IPSec
1.5.5.1 GRE overview
1.5.5.2 Lab: Basic GRE Tunnel
1.5.5.3 GRE over IPSec
1.5.5.4 Lab: IPSec in GRE
1.5.6 VTI (Virtual Tunnel Interface) / SVTI (Static Virtual Tunnel Interface)
1.5.6.1 Lab: Site-to-Site IPSec VPN with VTI / SVTI
1.5.7 More examples in Site-to-Site VPN
1.5.7.1 Lab: Cert-Based IPSec Site-to-Site VPN
1.5.8 More examples in EIGRP under point-to-point tunnelled environment
1.5.9 High Availability in IPSec VPN
1.5.9.1 SSO (Stateful Switchover)
1.5.9.2 Lab: High Availability in IPSec VPN: Topology building
1.5.9.3 Lab: High Availability in IPSec VPN: Create IKE policies, Transform Set and Crypto ACL
1.5.9.4 Lab: High Availability in IPSec VPN: SSO
2 IPSec VPN in ASA
2.1 Configuration Logics of IPSec VPN in ASA by “vpnsetup”
2.1.1 Lab: vpnsetup: site-to-site
2.1.2 Lab: vpnsetup: ipsec-remote-access
2.1.3 Lab: vpnsetup: l2tp-remote-access
2.1.4 Lab: vpnsetup: ssl-remote-access
2.2 Lab: Configure Site-toSite IPSec VPN between ASA and IOS – PSK
2.3 Lab: Verify the configurations in ASDM
2.3.1 Anti-replay window size
2.4 Lab: Configure Site-toSite IPSec VPN between ASA and IOS – Cert
3 Troubleshooting IPSec VPN
3.1 IKE Phase 1 Troubleshooting
3.2 IKE Phase 2 Troubleshooting
3.3 Fragmentation Problems in IPSec VPN
4 DMVPN (Dynamic Multipoint VPN)
4.1 Introduction to DMVPN
4.2 mGRE (multipoint GRE)
4.3 NHRP (Next Hop Resolution Protocol)
4.4 Routing in DMVPN
4.5 DMVPN phase 1
4.6 DMVPN phase 2
4.7 Single Hub DMVPN phase 1 and phase 2 labs
4.7.1 Lab: Single Hub DMVPN: Topology Building
4.7.2 Lab: Single Hub DMVPN Phase 1
4.7.3 Lab: Single Hub DMVPN Phase 1 with EIGRP
4.7.4 Lab: Single Hub DMVPN Phase 1 with OSPF (with more routes)
4.7.5 Lab: Single Hub DMVPN Phase 1 with OSPF (with lesser routes)
4.7.6 Lab: Single Hub DMVPN Phase 2
4.7.7 Lab: Single Hub DMVPN Phase 2 with EIGRP
4.7.8 Lab: Single Hub DMVPN Phase 2: Route summarization breaks DMVPN phase 2
4.8 DMVPN phase 3
4.8.1 Lab: Single Hub DMVPN phase 3
4.9 Apply IPSec in DMVPN
4.9.1 Lab: Apply IPSec in Single Hub DMVPN
4.10 if-state nhrp and backup tunnel interface
4.10.1 Lab: if-state nhrp and backup tunnel interface
4.11 MTU and MSS in DMVPN
4.11.1 MTU in DMVPN
4.11.2 MSS in DMVPN
4.11.3 Lab: Configure MTU and MSS in Single Hub DMVPN
4.12 Dual Hub DMVPN
4.12.1 Lab: Dual Hub DMVPN Phase 3
4.12.2 Lab: Dual Hub DMVPN Phase 3 with EIGRP
4.12.3 Lab: Apply IPSec in Dual Hub DMVPN
4.13 Configurations of all devices
4.13.1 Router1 (Hub router)
4.13.2 Router2 (Hub router)
4.13.3 Router3 (Spoke router)
4.13.4 Router4 (Spoke router)
4.13.5 Router5 (Internet router)
4.14 Summary of DMVPN Phase 1, Phase 2 and Phase 3 configurations
5 GET (Group Encryption Transport) VPN
5.1 Introduction to GET VPN
5.2 Benefits of GET VPN
5.3 Technologies in GET VPN
5.3.1 Group Members
5.3.2 Key Servers
5.3.3 GDOI Protocol
5.3.4 Group SA
5.3.5 Rekey Process
5.4 Basic Mutlicast Concepts
5.4.1 Lab: Basic Multicast Concepts
5.5 Basic Multicast Routing Concepts
5.5.1 Lab: Basic PIM-SM
5.6 GET VPN Configuration Procedures
5.6.1 Lab: GET VPN with multicast rekey
5.7 More about rekey concepts
5.7.1 Lab: Experiencing Re-Key Process (multicast rekey)
5.7.2 Lab: Unicast rekey
6 SSL VPN
6.1 SSL VPN Overview
6.2 Three Modes of SSL VPN
6.3 IOS SSL VPN
6.3.1 Login Page of SSL VPN
6.3.2 Lab: Basic SSL VPN
6.3.3 Lab: Basic SSL VPN with virtual-host concept.
6.3.4 Lab: Configure bookmarks in SSL VPN
6.3.5 Lab: File access and file browsing in SSL VPN
6.3.6 Lab: Thin Client
6.3.7 Lab: Tunnel Mode with AnyConnect
6.4 ASA SSL VPN
6.4.1 Lab: SSL VPN: Modify ASDM Port
6.4.2 Lab: SSL VPN: Clientless Mode
6.4.3 Lab: SSL VPN: Tunnel Mode (Smart Tunnel)
6.4.4 Webtype Access-List
6.4.4.1 Lab: SSL VPN: Webtype Access-List
6.4.5 Lab: configure bookmarks in ASDM
6.4.6 Lab: ASA SSL VPN with AnyConnect
6.4.7 Secure Desktop and prelogin assessment (Prelogin Policy)
6.4.7.1 Lab: Secure Desktop and prelogin assessment (Prelogin Policy)
6.4.8 Secure Desktop, host scan and dynamic access policy (DAP)
6.4.8.1 Lab: Dynamic access policy (DAP)
6.5 SSO in SSLVPN
6.6 Browser Plug-ins SSLVPN
6.7 HTTP proxy in SSL VPN
6.8 Trusted network detection in SSL VPN
6.9 Troubleshooting tips in SSL VPN
7 Next Generation Encryption (NGE)
7.1 Suite B cryptography
7.2 Galois/Counter Mode (GCM)
8 IKEv2 and Flex VPN
8.1 IKEv2
8.2 Site-to-site Flex VPN
8.2.1 Compare FlexVPN, DMVPN, crypto map implementation
8.2.2 FlexVPN components
8.2.2.1 IKEv2 proposal
8.2.2.2 IKEv2 Policy
8.2.2.3 IKEv2 Profile
8.2.2.4 IKEv2 Key Ring
8.2.2.5 IKEv2 Authorization Policy
8.2.3 Smart defaults
8.2.3.1 Lab: Smart Defaults
8.2.3.2 Lab: Configure site-to-site Flex VPN by using smart defaults with symmetric authentication
8.2.3.3 Lab: Configure site-to-site Flex VPN by using smart defaults with asymmetric authentication
8.2.4 Advanced site-to-site Flex VPN topics
8.2.4.1 Lab: IOS-CA in IOS 15.x
8.2.4.2 Lab: Configure Router5 to obtain a certificate from IOS CA
8.2.4.3 Lab: Configure site-to-site Flex VPN by custom IKEv2 configurations with asymmetric authentication (Router4: PSK, Router5: RSA-SIG)
8.2.4.4 Lab: Configure IPv6 site-to-site Flex VPN
8.3 Hub and spokes Flex VPN
8.3.1 Lab:Flex VPN server with aaa authorization
8.3.2 Lab:Flex VPN client with aaa authorization
8.4 IKEv2 in ASA
8.4.1 Demonstration: Site-to-site VPN by IKEv2 in ASA
9 Appendix: Configure IPSec VPN with pre-shared keys by using tunnel group in ASA
SISAS
1 AAA Concepts
1.1 Introduction to AAA
1.1.1 Authentication
1.1.2 Authorization
1.1.3 Accounting
1.2 AAA Protocols
1.2.1 RADIUS
1.2.1.1 Summary of RADIUS
1.2.2 TACACS+
1.2.2.1 Summary of TACACS+
1.2.3 Compare RADIUS and TACACS+
1.3 Extensible Authentication Protocol (EAP)
1.3.1 EAP-MD5
1.3.2 EAP-TLS
1.3.3 EAP-PEAP
1.3.4 EAP-FAST
2 AAA with Cisco Secure ACS
2.1 Introduction to Cisco Secure ACS
2.2 IEEE 802.1x
2.2.1 IEEE 802.1x architecture
2.2.2 Lab: AAA Authentication in IEEE 802.1x with Cisco Secure ACS
2.2.3 Lab: AAA Authorization in IEEE 802.1x with Cisco Secure ACS
2.2.4 Lab: AAA Accounting in IEEE 802.1x with Cisco Secure ACS
2.2.5 Lab: Debugging AAA and RADIUS activities
2.3 AAA in IOS
2.3.1 Lab: Enable telnet access by using AAA in Cisco Routers (Authentication)
2.3.2 Lab: Enable telnet access by using AAA in Cisco Routers (Authorization)
2.3.3 Command authorization and accounting
2.3.3.1 Lab: Command authorization
2.3.3.2 Lab: Command accounting
2.4 AAA in ASA
2.4.1 Lab: Local AAA for telnet authentication
2.4.2 Lab: Local AAA for SSH authentication
2.4.3 Lab: Local AAA for ASDM authentication
2.4.4 Lab: Local AAA for Console authentication
2.4.5 Lab: Local AAA for Enable authentication
2.4.6 Lab: AAA authentication for telnet authentication by using Cisco Secure ACS
2.4.7 Lab: AAA authentication for SSH authentication by using Cisco Secure ACS
2.4.8 Lab: AAA authentication for ASDM authentication by using Cisco Secure ACS
2.5 ACS design
2.5.1 Basic ACS deployment
2.5.2 Split ACS deployment
3 Cisco ISE (Identity Services Engine)
3.1 Introduction to Cisco ISE
3.2 ISE solution components
3.2.1 Infrastructure components
3.2.1.1 MAB
3.2.1.2 IEEE 802.1X
3.2.1.3 Web Authentication
3.2.1.4 CoA
3.2.1.5 VLAN
3.2.1.6 Downloadable ACL
3.2.1.7 SGA
3.2.1.8 IOS Device Sensor
3.2.2 Policy components
3.2.3 Endpoint components
3.3 ISE personas
3.4 ISE deployment phases
3.4.1 Monitor Mode
3.4.2 Low-Impact Mode
3.4.3 Closed Mode
3.5 ISE installation
3.6 Common ports used by ISE
3.7 ISE certificates
3.8 ISE admin access
3.9 ISE backup and restoration
3.10 Configure a catalyst switch to work with ISE
3.10.1 Lab: Enable HTTP / HTTPS Server
3.10.2 Lab: Configure AAA
3.10.3 Lab: Global radius configurations
3.10.4 Lab: Configure CoA (Change of Authorization)
3.10.5 Lab: ACLs for Monitor mode, Low-Impact mode and redirection
3.10.6 Lab: Configure global logging
3.10.7 Lab: Configure global 802.1X
3.10.8 Lab: Global Profiling
3.10.9 Lab: Interface configurations with flexible authentication
3.10.10 Lab: Enable 802.1X and MAB on a switchport
3.10.11 Lab: Implement authentication under Monitor mode
3.10.12 Lab: Implement authentication under Low-Impacted mode
3.10.13 Lab: Final configurations of all previous labs
3.11 Configure ISE to communicate with a catalyst switch
3.11.1 Configure a network device in ISE
3.11.2 Configure a user in ISE
3.12 ISE Profiling
3.12.1 Introduction to profiling
3.12.2 Probes
3.12.3 Configure ISE to enable profiling
3.12.4 HTTP Probe
3.12.4.1 Configure ISE to enable HTTP probe
3.12.5 Probes by DHCP
3.12.5.1 DHCP SPAN probes
3.12.5.2 DHCP probes
3.12.5.3 Configure ISE to enable DHCP probe
3.12.6 NetFlow Probe
3.12.6.1 Configure ISE to enable Netflow probe
3.12.7 RADIUS Probe
3.12.7.1 Configure ISE to enable RADIUS probe
3.12.8 Network Scan (NMAP) Probe
3.12.8.1 Configure ISE to enable Network Scan (NMAP) probe
3.12.9 DNS Probe
3.12.9.1 Configure ISE to enable DNS probe
3.12.10 Probes by using SNMP
3.12.10.1 SNMPTrap Probe
3.12.10.2 SNMPQuery Probe
3.12.10.3 Configure ISE to enable DNS probe
3.12.11 Device Sensor
3.12.12 Configure ISE to view the result of profiling
3.12.13 Profiling policy and profiling conditions
3.12.14 ISE TCP Dump for troubleshooting profiling packets
3.12.14.1 Configure ISE TCP Dump
3.12.15 ISE Profiler CoA (Change of Authorization)
3.12.15.1 Configure global CoA globally in ISE
3.13 ISE Authentication
3.13.1 Authentication policy
3.13.2 Authentication conditions
3.13.3 Allowed protocols
3.13.4 Identity stores
3.13.4.1 Configure ISE to join Active Directory
3.13.5 If ISE authentication fails
3.13.5.1 Reject
3.13.5.2 Continue
3.13.5.3 Drop
3.13.6 Configure MAB (MAC Authentication Bypass) in ISE
3.13.7 Configure Dot1X (EAP-MD5) in ISE
3.13.8 Configure Dot1X (PEAP with MSCHAPv2) in ISE
3.13.9 Tunneled EAP Types
3.13.9.1 EAP Chaining with EAP-FASTv2
3.14 ISE Authorization
3.14.1 Introduction to ISE authorization
3.14.2 ISE authorization policy
3.14.2.1 Conditions
3.14.2.2 Authorization profile
3.14.3 Create an identity group for Apple-iPhone in ISE
3.14.4 Create a custom identity group for “Router4”
3.14.5 Configure downloadable ACL (dACL) in ISE
3.14.6 Configure authorization profile in ISE
3.14.7 Configure authorization policy in ISE
3.14.8 Verify ISE authentication and authorization policy
3.14.9 Configure dynamic VLAN assignment in ISE
3.14.10 More about conditions in an authorization policy
3.15 ISE Guest Management
3.15.1 Portals
3.15.1.1 Guest portal
3.15.1.2 Sponsor web portal
3.15.1.3 Device registration portal
3.15.2 Configure central web authentication (CWA) for sponsors and guests in ISE
3.15.2.1 Configure portals theme in ISE
3.15.2.2 Configure ports used in portals in ISE
3.15.2.3 Configure sponsor authentication servers in ISE
3.15.2.4 Configure and customize language template for the sponsor portal
3.15.2.5 Configure Guest Detail Policy in ISE
3.15.2.6 Configure and customize language template for the guest portal in ISE
3.15.2.7 Configure the default guest portal in ISE
3.15.2.8 Configure guest portal policy in ISE
3.15.2.9 Configure guest password policy in ISE
3.15.2.10 Configure time profile in ISE
3.15.2.11 Configure username policy in ISE
3.15.2.12 Configure sponsor group in ISE
3.15.2.13 Create an identity group (user) for sponsor group policy in ISE
3.15.2.14 Configure sponsor group policy in ISE
3.15.2.15 Configure an authentication policy for central web redirection in ISE
3.15.2.16 Configure a dACL for central web authentication in ISE
3.15.2.17 Configure a dACL for guests (after login) in ISE
3.15.2.18 Configure an authorization profile for central web authentication in ISE
3.15.2.19 Configure an authorization profile for guests (after login) in ISE
3.15.2.20 Create an authentication policy for central web authentication in ISE
3.15.2.21 Create an authorization policy for guests (after login) in ISE
3.15.2.22 Configure Switch3’s g1/0/3 to allow central web authentication
3.15.2.23 Verify if clients can be redirected to the guest portal
3.15.2.24 Verify if self-registration is workable or not
3.15.2.25 Verify if the sponsor portal runs properly
3.15.2.26 Create and verify a guest account created in the sponsor portal
3.16 ISE posture
3.16.1 Introduction to ISE posture
3.16.2 ISE posture assessment process
3.16.3 Configuration steps
3.16.3.1 Configure global posture settings in ISE
3.16.3.2 Configure posture conditions
3.16.3.3 Configure posture requirement in ISE
3.16.3.4 Configure posture policy in ISE
3.16.3.5 Configure conditions (NonCompliant) for authorization policy in ISE
3.16.3.6 Configure conditions (Compliant) for authorization policy in ISE
3.16.3.7 Configure conditions (Unknown) for authorization policy in ISE
3.16.3.8 Create a dACL for NonCompliant in ISE
3.16.3.9 Create a dACL for Compliant in ISE
3.16.3.10 Create a dACL for Unknown in ISE
3.16.3.11 Create an authorization profile for NonCompliant in ISE
3.16.3.12 Create an authorization profile for Compliant in ISE
3.16.3.13 Create an authorization profile for Unknown in ISE
3.16.3.14 Disable irrelevant rules in the authorization policy in ISE
3.16.3.15 Create a rule (Unknown) in the authorization policy in ISE
3.16.3.16 Create a rule (NonCompliant) in the authorization policy in ISE
3.16.3.17 Create a rule (Compliant) in the authorization policy in ISE
3.16.3.18 Final check before installing NAC agent
3.16.3.19 Install and configure NAC agent
3.16.3.20 Verify ISE posture configurations
4 MACSec
4.1 Introduction to MACSec
4.2 Downlink MACSec
4.2.1 Configuration combinations and their results
4.2.2 Authentication host mode in switches
4.2.3 MKA policy
4.2.4 Configure downlink MACSec in ISE
4.2.5 Configure switchports in switches
4.2.6 Install Anyconnect Network Access Manager in a PC
4.2.7 Create a profile in AnyConnect Network Access Manager
4.2.8 Perform 802.1X authentication and MACSec
4.3 Uplink MACSec
4.3.1 Configure uplink MACSec between switches
5 TrustSec
5.1 Introduction to TrustSec
5.2 TrustSec classification
5.2.1 Inline tagging by ISE (Dynamically assignment)
5.2.2 IP to SGT (Statically assignment)
5.2.2.1 Lab: IP to SGT (Statically assignment)
5.3 TrustSec propagation
5.3.1 Inline (native SGT propagation)
5.3.1.1 Lab: Configure inline propagation
5.3.2 SXP (SGT Exchange Protocol)
5.3.3 Lab: SXP (SGT Exchange Protocol)
5.4 TrustSec enforcement
6 Miscellaneous topics
6.1 Radius aggressive failover feature in WLC (Wireless LAN Controller)
6.2 802.11i in WLC
6.3 MFP (Management Frame Protection)
6.4 Client Provisioning in ISE
6.5 AAA Override in WLC
6.6 RADIUS NAC in WLC
6.7 Cisco wireless IPS solution (wIPS)
7 Appendix 1: Authentication Proxy in IOS
7.1 Introduction to Authentication Proxy
7.2 Authentication Proxy process
7.3 Configuration Procedures
7.4 Lab: Authentication Proxy
8 Appendix 2: Cut-through Proxy in ASA
8.1 Introduction to Cut-through Proxy
8.2 Lab: Cut-through Proxy
9 Appendix 3: Policy-based NAT in IOS
9.1 Introduction to Policy-based NAT
9.2 Lab: Policy-based NAT
SITCS
(本課程的課堂錄影隨時睇會教授 300-207 版本,而模擬考試題目於 2017 年 1 月 1 日或之後則會提供 300-210 版本,令學員能考 300-210 考試。)
1 Cisco Cloud Web Security (CWS)
1.1 History of Cisco Cloud Web Security (CWS)
1.2 Cisco Cloud Web Security (CWS) operations
1.3 Cisco CWS demonstration
1.3.1 Demonstration: Login to Scan Center
1.3.2 Demonstration: Generate a company key
1.3.3 Demonstration: Configure a Cisco ISR G2 to enable CWS
1.3.4 Demonstration: Verify if the PC is protected by Cisco Cloud Web Security
1.3.5 SearchAhead
1.3.5.1 Demonstration: SearchAhead
1.3.6 Demonstration: Global config
1.3.7 Demonstration: Blocking gambling web sites (Create a new filter)
1.3.8 Demonstration: Blocking gambling web sites (Create a new filter rule)
1.3.9 Demonstration: Blocking gambling web sites (Verification)
1.3.10 Demonstration: Reports
1.3.11 Demonstration: Policy trace
1.3.12 Demonstration: A white list
1.3.13 Demonstration: Application Visibility and Control (AVC)
1.3.14 TShoot CWS in Cisco ISR G2
2 Cisco Email Security Appliance (Cisco ESA)
2.1 Introduction to ESA
2.1.1 Inbound email message flow with ESA
2.1.2 Outbound email message flow with ESA
2.1.3 Filtering Spam
2.1.3.1 Reputation-Based filtering
2.1.3.2 Context-Based Filtering
2.1.4 Viruses and Malware with outbreak filters
2.2 Deployment
2.3 CLI in ESA
2.3.1 adminaccessconfig
2.3.2 sslconfig
2.3.3 interfaceconfig
2.4 System Setup Wizard (SSW)
2.5 Default anti-spam actions
2.6 Incoming SMTP connections
2.6.1 Demonstration: Mail Flow Policy
2.7 Message Tracking
2.7.1 Demonstration: Message Tracking
2.8 tophosts
2.8.1 Demonstration: tophosts
2.9 trace
2.9.1 Demonstration: trace
2.10 Message Filter
2.10.1 Demonstration: Message Filter
2.11 ESA Cluster / centralized management
2.11.1 The meaning of “cluster”
2.11.2 Cluster requirements
2.11.3 Create a CM cluster
2.11.4 Join a CM cluster
2.12 Cisco IronPort Hybrid Email Security
2.13 Cisco Registered Envelope Service (CRES)
2.14 LDAP in ESA
3 Cisco Web Security Appliance (Cisco WSA)
3.1 Introduction to WSA
3.2 Deployment
3.2.1 Transparent proxy mode and explicit proxy mode
3.2.2 Secure access to WSA
3.3 WSA model comparison
3.4 Compare Cisco WSA with Cisco CWS
3.5 Default configuration in WSA
3.6 Demonstrations
3.6.1 Demonstration: System Setup Wizard for WSA initialization
3.6.2 Demonstration: Verify proxy configuration
3.6.3 Demonstration: Blocking gambling sites by WSA
3.6.4 Demonstration: Custom URL category to block “systematic.com.hk”
3.6.5 Demonstration: Application Visibility and Control to block Facebook
3.7 HTTPS Inspection
3.7.1 Demonstration: HTTPS proxy
3.8 strictssl
3.8.1 Demonstration: strictssl
3.9 Reports in WSA
3.9.1 Demonstration: Reports in WSA
3.10 WCCP (Web Cache Communication Protocol)
3.10.1 Redirect methods
3.10.1.1 WCCP GRE
3.10.1.2 WCCP L2
3.10.2 Intercept methods
3.10.3 Assignment methods
3.10.3.1 Hash assignment
3.10.3.2 Mask assignment
3.10.4 Service groups
3.10.5 Demonstration: WCCP between ASA and WSA
4 Cisco ASA Next-Generation Firewall Services (CX)
4.1 Deployment
4.2 Four architectural constructs in ASA CX
4.3 Application visibility and control in NGFW
4.4 ASA CX Module
4.5 Traffic flow of ASA and ASA CX
4.6 Management Interface of ASA CX
4.6.1 ASA 5585-X
4.6.2 ASA 5512-X through ASA 5555-X
4.7 Installing the Software Module
4.8 Initialize ASA CX
4.9 Redirecting Traffic to the ASA CX Module
4.10 Block Malware Using Web Reputation
4.11 Managing SSL/TLS Traffic Flows
4.12 Cisco Prime Security Manager (PRSM)
5 Cisco Intrusion Prevention System (Cisco IPS)
5.1 Cisco IPS Series Sensors
5.2 Basic Sensor Initialization
5.2.1 Display sensor information
5.2.2 Display sensor current configurations
5.2.3 Erase all current configurations
5.2.4 Reboot the sensor
5.2.5 Default configurations of sensors
5.2.6 Demonstration: Configure hostname in the sensor
5.2.7 Demonstration: Configure IP address and subnet mask in the sensor
5.2.8 Demonstration: Configure hostname, IP, subnet mask and gateway in 6.x / 7.x sensors
5.2.9 Demonstration: Access to sensor through HTTPS
5.2.10 Demonstration: Access to sensor 6.x / 7.x through IDM / IPS Manager Express
5.2.11 Demonstration: Access to sensor through SSH
5.2.12 Demonstration: Configure NTP on Sensor
5.2.13 Demonstration: Configure NTP on Sensor 6.x / 7.x
5.2.14 Demonstration: Configure telnet service in sensors
5.2.15 Demonstration: Configure Telnet Service in Sensor 6.x / 7.x
5.2.16 SNMP configurations
5.2.16.1 Demonstration: Configure SNMP in IPS 6.x / 7.x
5.3 Sensor interfaces
5.3.1 Command and Control (C&C) Interface
5.3.2 Sensing Interfaces
5.3.3 Promiscuous mode
5.3.3.1 Demonstration: Configure sensing interface and interface group
5.3.3.2 Demonstration: Enable senor physical interface in IPS 6.x / 7.x
5.3.4 Inline mode
5.3.4.1 Demonstration: Enable Inline interface-pair in IPS 6.x / 7.x
5.3.4.2 Demonstration: Enable Inline VLAN-Pair interfaces in IPS 6.x / 7.x
5.3.4.3 Demonstration: Enable Inline VLAN Group (Promiscuous) in IPS 6.x / 7.x
5.3.5 Hardware bypass
5.4 Virtual sensors
5.4.1 Introduction to virtual sensors
5.4.2 Demonstration: Configure virtual sensor in promiscuous interface in IPS 6.x / 7.x
5.4.3 Demonstration: Configure virtual sensor in Inline VLAN-Pair in IPS 6.x / 7.x
5.4.4 Demonstration: Configure virtual sensor in Inline VLAN-group in IPS 6.x / 7.x
5.4.5 Inline TCP session tracking modes
5.4.6 Normalizer modes
5.5 Signature tuning
5.5.1 Introduction to signature tuning
5.5.2 Demonstration: Enable ICMP echo reply (2000) signature through GUI
5.5.3 Demonstration: Enable ICMP echo request (2004) signature by using CLI
5.5.4 Demonstration: Enable ICMP echo request and echo reply signature in IPS 6.x / 7.x
5.6 SPAN and RSPAN
5.6.1 Local SPAN
5.6.2 Remote SPAN (RSPAN)
5.6.2.1 Demonstration: Remote SPAN (RSPAN) with sensor
5.7 Event counting and summarization concepts
5.7.1 Event counting
5.7.2 Event summarization
5.8 Custom signatures
5.8.1 Introduction to custom signatures
5.8.2 Demonstration: Custom signatures
5.8.3 Demonstration: Detail understanding the TCP Reset structure
5.8.4 Demonstration: Custom signature with routing scenario
5.8.5 Demonstration: Configure a custom signature for IPS Software 6.x / 7.x
5.9 IP Logging
5.9.1 Demonstration: IP Logging
5.9.2 Demonstration: Copy the log file to FTP Server
5.9.3 Demonstration: Manual IP Logging for a specific IP address
5.9.4 Demonstration: Stopping active IP logging
5.9.5 Demonstration: IP Logging in IPS Software 6.x / 7.x
5.10 Attack Response Controller (ARC) technologies
5.10.1 Type of blocking
5.10.2 Blocking devices
5.10.3 Attack response controller (ARC) for rate limiting
5.10.4 Demonstration: Configure blocking by sensor SSH 3DES connection in IPS 6.x / 7.x
5.10.5 Demonstration: Configure rate limiting by sensor in IPS 6.x / 7.x
5.10.6 Demonstration: Configure blocking by sensor SSH 3DES connection
5.11 Risk Rating Calculation
5.11.1 Signature Fidelity Rating (SFR) / Fidelity Rating (FR)
5.11.2 Target Value Rating (TVR)
5.11.3 Attack Relevancy Rating (ARR)
5.11.4 Promiscuous Delta (PD)
5.11.5 Watch List Rating (WLR)
5.11.6 RR (Risk Rating) equation
5.12 Event action override
5.12.1 Demonstration: Event action override
5.13 Event action filter
5.13.1 Demonstration: Event action filter
5.14 Anomaly Detection (AD)
5.14.1 Introduction to Anomaly Detection
5.14.2 AD Zones
5.14.3 Anomaly Detection Logics
5.14.4 Anomaly Detection Modes / Anomaly Operation Modes
5.14.4.1 Learning Accept Mode
5.14.4.2 Detect Mode
5.14.4.3 Inactive Mode
5.15 Global correlation inspection and Reputation Filtering
5.15.1 Global correlation inspection
5.15.2 Reputation filtering
5.16 Best practices in IPS solutions
5.17 Final demonstration in IPS
6 Cisco IntelliShield Alert Manager Service
Additional Readings
1 Security with Cisco Routers and Switches
1.1 STP Security
1.1.1 Rouge Root Bridge
1.1.2 Rouge BPDU Message
1.1.3 BPDU DoS (Denial of Service)
1.2 HSRP Security
1.2.1 Lab: Basic HSRP
1.2.2 Lab: HSRP MD5 Authentication
1.3 VRRP Security
1.3.1 Lab: Basic VRRP
1.3.2 Lab: VRRP MD5 Authentication
1.4 Flexible Packet Matching (FPM)
1.4.1 Today’s filtering challenges
1.4.2 FPM Configuration Procedures
1.4.3 Protocol Header Description File (PHDF)
1.4.4 Example in FPM: Configuring FPM for MyDoom Packets
1.4.5 Lab: FPM
1.5 Appliance Trust
1.6 Control Plane Security
1.6.1 Lab: Input Control Plane Security
1.6.2 Lab: Output Control Plane Security
1.7 Transparent Zone Base Firewall
1.7.1 Today’s challenges
1.7.2 Brainstorming 1
1.7.3 Brainstorming 2
1.7.4 Bridging overview
1.7.5 Bridging operations
1.7.6 IRB Bridging
1.7.7 Lab: Configure IRB Bridging
1.7.8 Zone Base Firewall under IRB bridging
1.7.9 Lab: Transparent Zone Base Firewall
2 ASA
2.1 IP Routing in ASA
2.1.1 Basic Routing Concepts
2.1.2 Static Routing
2.1.2.1 Lab: ASA Static Routing
2.1.2.2 Lab: Simple Load Balancing by Static Routes
2.1.3 Service Level Agreement (SLA) in ASA
2.1.3.1 Static Routing with SLA
2.1.4 RIP
2.1.4.1 Lab: RIPv1 in ASA
2.1.4.2 Lab: RIPv2 in ASA
2.1.4.3 Lab: default gateway advertisement by RIP in ASA
2.1.4.4 Lab: RIPv1 and RIPv2 coexist in ASA
2.1.4.5 Lab: RIP plain text authentication in ASA
2.1.4.6 Lab: RIP MD5 authentication in ASA
2.1.5 OSPF (Open Shortest Path First)
2.1.5.1 Lab: Single Area OSPF
2.1.5.2 Lab: Multi-Area OSPF
2.1.5.3 Lab: Advertise default gateway via OSPF in ASA
2.1.5.4 Special OSPF Network Type in ASA
2.1.5.5 Lab: OSPF Point-to-Point Non-Broadcast network type in ASA
2.1.5.6 Virtual Link
2.1.5.7 Lab: Virtual Link in ASA
2.1.5.8 OSPF Authentication
2.1.5.9 Lab: OSPF Plain Text authentication
2.1.5.10 Lab: OSPF MD5 authentication
2.1.6 EIGRP
2.1.6.1 Lab: Configure EIGRP in ASA
2.1.6.2 EIGRP Authentication
2.1.6.3 Lab: Enable EIGRP Authentication in ASA
2.2 IP Multicast in ASA
2.2.1 Lab: Multicast in ASA
2.3 NAT in ASA before software 8.3
2.3.1 Demonstration: Dynamic NAT with overload
2.3.2 Demonstration: Static NAT
2.3.3 Demonstration: Static NAT (Port redirection)
2.3.4 Demonstration: Identity NAT
2.3.5 Demonstration: Policy NAT
2.4 Quality of Service (QoS) in ASA
2.4.1 QoS Support in ASA
2.4.2 QoS configuration logics in ASA
2.4.3 Lab: QoS Policing in ASA
2.4.4 Lab: QoS Policing in Router2
2.4.5 Lab: QoS Shaping in ASA1
2.4.6 Lab: QoS Priority Queue in ASA
2.5 Advanced Topics in Multiple Contexts
2.5.1 Multiple Contexts on Transparent Firewall
2.5.1.1 Demonstration: Multiple Contexts in Transparent Firewall
2.5.2 Multiple Contexts with shared interface
2.5.2.1 Demonstration: Configure a shared interface (e0/0.100) for multiple contexts
2.5.3 Concepts of default class
2.5.3.1 Demonstration: Configure Resource Limit on the context
2.6 Active / Active Failover
2.6.1 Demonstration: Active / Active Failover
2.7 Password Recovery in ASA
2.7.1 Demonstration: Password Recovery in ASA
2.8 Configuration disclosure avoidance
2.8.1 Demonstration: Disable Password-Recovery
2.9 High End ASA Initialization
2.9.1 Demonstration: Initialize High End ASA
2.9.2 Management Interface
2.9.2.1 Demonstration: Management Interface
2.9.3 Subinterface (Trunking) in ASA
2.9.3.1 Demonstration: ASA Subinterface
3 VPN
3.1 IOS EZVPN
3.1.1 EZVPN Components
3.1.1.1 EZVPN Client
3.1.1.2 EZVPN Remote
3.1.1.3 EZVPN Server
3.1.2 Tunnel Building Process
3.1.3 Concept of split tunnelling
3.1.4 Concept of RRI (Reverse Route Injection)
3.1.5 Lab: Configure IOS EZVPN Server and EZVPN Client
3.1.6 Lab: Additional Features in EZVPN
3.1.7 EZVPN Server with DVTI
3.1.7.1 Lab: EZVPN Server with DVTI
3.2 IOS EZVPN Remote
3.2.1 Mode of EZVPN Remote
3.2.2 Lab: EZVPN Remote (Client Mode with manual tunnel initialization)
3.2.3 Lab: EZVPN Remote (Client Mode with auto tunnel initialization)
3.2.4 Lab: EZVPN Remote (Network Extension Mode with auto tunnel initialization)
3.2.5 Lab: EZVPN Remote (Network Extension Plus Mode with auto tunnel initialization)
3.3 Authentication in EZVPN Remote
3.3.1 Xauth in EZVPN
3.3.2 Lab: EZVPN Remote with Web Based Activation
3.4 ASA EZVPN
3.4.1 Lab: ASA EZVPN
3.5 ASA EZVPN Remote
3.5.1 Client Mode and NEM Mode
3.5.2 Lab: EasyVPN Remote in Client Mode
3.5.3 Lab: EasyVPN Remote in NEM Mode
3.6 NAT with IPSec VPN
3.6.1 Lab: Easy VPN with dynamic NAT environment
 付款。
付款。