(在家觀看 = 0%,在校觀看 = 100%)
100% 在校觀看日期及時間:
自由選擇,點選以下地區觀看辦公時間及位置
課時: 96 小時
享用時期: 32 星期。進度由您控制,可快可慢。
課堂錄影導師:Larry
在校免費試睇:首 3 小時,請致電以上地點與本中心職員預約。
半費重考。開始觀看最後 1 堂之 1 個月內為保障期限。請務必向本中心購買考試券。
本課程提供在校免費重睇及導師解答服務。
(在家觀看 = 100%,在校觀看 = 0%)
100% 在家觀看日期及時間:
每天 24 小時全天候不限次數地觀看
課時: 96 小時
享用時期: 32 星期。進度由您控制,可快可慢。
課堂錄影導師:Larry
在校免費試睇:首 3 小時,請致電以上地點與本中心職員預約。
半費重考。開始觀看最後 1 堂之 1 個月內為保障期限。請務必向本中心購買考試券。
本課程提供導師解答服務。
由於電腦網絡能帶給公司很多益處 (如共用印表機、檔案、資料庫、寬頻上網等,又可設定各式各樣的保安措施),再加上 Internet (互聯網) 及 Cloud (雲端) 的發展蓬勃,故此有很多公司,不論大、中或小型,都紛紛將公司的電腦網絡化,以致 Microsoft 的網絡產品大受歡迎,形成市場對 Microsoft 網絡人材的強大需求,所以他們的市場價值亦相對其他行業為高。

Microsoft 已於 2021年 9月 1日推出了 Windows Server 2022,繼 Windows Server 2016 勢必成為主流伺服器操作系統,並成為 Microsoft 下一個經 Long-Term Servicing Channel (LTSC) 售賣並長期支援的主要版本。而熟識 Windows Server 2022 日常管理及先進技術,更是企業資訊科技解決方案架構師 (Enterprise I.T. Solutions Architect) 不可缺少的必要技能。
新版本的 Windows Server 2022 帶來了以下重大優勢:
Advanced multi-layer security:
Windows Server 2022 通過 Secured-core 服務器和安全連接,提供了多層安全性。Secured-core 服務器意指由 Microsoft 的硬件合作夥伴提供硬件、固件 (firmware) 和驅動程序,以幫助客戶加強其關鍵系統的安全性。
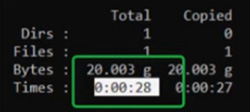
Hybrid capabilities with Azure:
混合或多雲環境中的客戶,可以通過連接 Azure Arc,使用更新管理、Azure Monitor、安全中心等功能,從而利用本地 Windows Server 2022 的雲服務!
此外,你還可以利用 Windows Server 2022 的 File Server 增強功能,例如 SMB (Server Message Block) 壓縮。SMB 壓縮通過在網絡傳輸時壓縮數據來改進檔案傳輸效能。
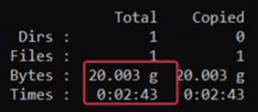
由 Microsoft 工程人員的實際測試顯示,於 1Gbps 的網絡使用 Windows Server 2022 SMB 壓縮 (右圖) 來傳送大量檔案(約20GB),只需 28 秒,比未升級至 Windows Server 2022 前 (左圖) 所需的 2 分 43 秒大幅下降!
 |
 |
Flexible application platform:
Windows Server 2022 帶來了可擴展性改進,例如支持 48TB 記憶體 (memory) 和 2,048 個邏輯內核 (logical cores),並可在 64 個實體插槽 (physical sockets) 上運行。再者,對 Windows 容器亦帶來了許多附加改進,例如提高 Windows Containers 的應用程序兼容性,包括 HostProcess Containers 配置,支持 IPv6 Dual Stack,並通過 Calico Container Networking 實現一致的 Network Policy,並為 Azure Stack HCI 上的 Azure Kubernetes 服務 (AKS) 和 Azure Cloud 上的 AKS 帶來新功能。
根據 Microsoft 意見,Enterprise I.T. Solutions Architect 級別的專業人員應該具備實施和管理自設 (On-Premises) 和混合 (Hybrid) 解決方案的專業知識,例如身份、管理、計算、網絡和存儲。
他們還是執行與安全、遷移、監控、高可用性、故障排除和災難恢復相關任務的專家,並需使用管理工具和技術,包括 Windows Admin Center、PowerShell、Azure Arc、Docker Containers、Kubernetes 和 Windows Server 2022 Azure Virtual Machines。
An example of a Hybrid solution with Windows Server 2022
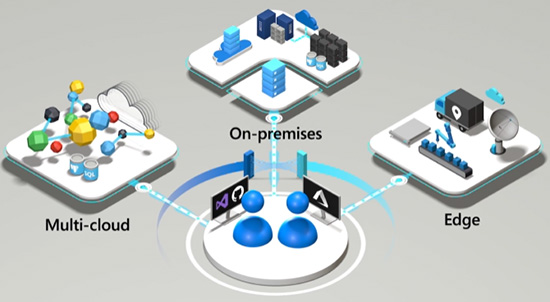
上述管理工具和技術還要與 Azure 自動化更新管理、Microsoft Defender for Identity、Azure 安全中心、Azure Migrate 和 Azure Monitor 配合使用。
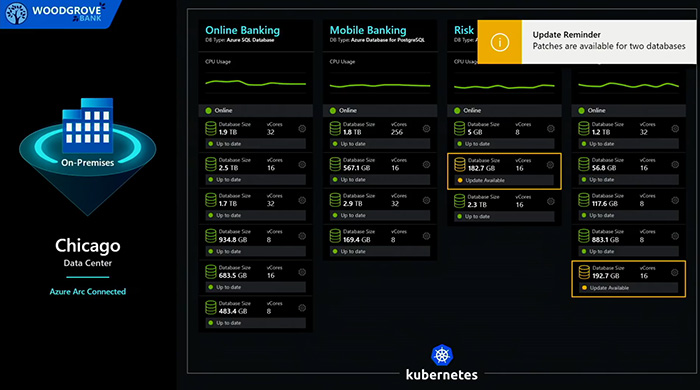
An example of Azure-Managed Automatic Update of Applications running on Windows Server 2022 at On-premises Networks
本中心推出全新的 Microsoft Certified Windows Server Hybrid Administrator Associate 認證課程,本課程籌備多時,精心編排,由上堂、溫習、實習、考試研習、做試題至最後考試,均為你度身訂造,作出有系統的編排。務求真正教識你,又令你考試及格。
| 課程名稱: |
Microsoft Certified Windows Server Hybrid Administrator Associate (2科 Windows Server 2022) 國際認可證書課程 (Full Track) - 簡稱:Windows Server 2022 Training Course (Full Track) |
| 課程時數: | 96 小時 (共 32 堂) |
| 適合人士: | 有志投身 I.T. 界的人士 |
| 授課語言: | 以廣東話為主,輔以英語 |
| 課程筆記: | 本中心導師親自編寫英文為主筆記,而部份英文字附有中文對照。 |
| 1. 模擬考試題目: | 本中心為學員提供模擬考試題目,每條考試題目均附有標準答案。 |
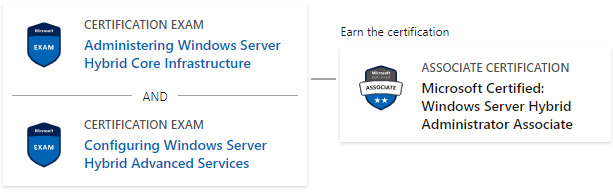
| 2. 時數適中: | 本中心的 Microsoft Certified Windows Server Hybrid Administrator Associate (2科 Windows Server 2022) 國際認可證書課程 (Full Track) 時數適中,有 96 小時。 令學員能真正了解及掌握課程內容,而又能於 4 個月內考獲以下 1 張國際認可證書:
Microsoft Certified: Windows Server Hybrid Administrator Associate 認證可幫助學員入職以下職位:
|
| 3. 導師親自編寫筆記: | 由本中心已擁有五項 MCITP,十多項 MCTS,MCSA 及 MCSE 資格,並有教授 Microsoft 相關課程 20年以上經驗的資深導師 Larry Chan 親自編寫筆記,絕對適合考試及實際管理之用,令你無須「死鋤」如字典般厚及不適合香港讀書格調的書本。 |
| 4. 一人一機上課: | 本課程以一人一機模式上課。 |
| 5. 考試合格保障: | 本中心為 Microsoft Certified Windows Server Hybrid Administrator Associate (2科 Windows Server 2022) 國際認可證書課程 (Full Track) 學員設有全部 2 科合格保障,包括:AZ-800 及 AZ-801。 以 AZ-800 為例,本中心學員於第一次考 AZ-800 若不合格,可申請
半費重考 AZ-800 一次,但必須符合下列的四項要求: 1. 本課堂出席率須達 85% 以上。 2. 學員必須於本中心應考 AZ-800 考試。 3. 學員於第一次應考 AZ-800 考試前,必須進行本中心的 AZ-800 試前測驗,並取得 90% 或以上的分數。 4. 於上課結束日之一個月內作出申請。 |
| 6. 免費重讀: | 傳統課堂學員可於課程結束後三個月內免費重看課堂錄影。 |
Microsoft 已公佈考生只要通過以下 2 個 Windows Server 2022 相關科目的考試,便可獲發 Microsoft Certified: Windows Server Hybrid Administrator Associate 國際認可證書:
| 考試編號 | 科目名稱 |
| AZ-800 | Administering Windows Server Hybrid Core Infrastructure |
| AZ-801 | Configuring Windows Server Hybrid Advanced Services |
以上 2 科,全部設有 “考試合格保障”。
本中心為Microsoft指定的考試試場。報考時請致電本中心,登記欲報考之科目考試編號、考試日期及時間
(最快可即日報考)。臨考試前要出示身份證及繳付每科HK$943之考試費。 考試不合格便可重新報考,不限次數。欲知道作答時間、題目總數、合格分數等詳細考試資料,可瀏覽本中心網頁 "各科考試分數資料"。 |
|
課程名稱:Microsoft Certified Windows Server Hybrid Administrator Associate (2科 Windows Server 2022) 國際認可證書課程 (Full Track) - 簡稱:Windows Server 2022 Training Course (Full Track) |
AZ-800 Administering Windows Server Hybrid Core Infrastructure (60 hrs)
1. Installing Windows Server 2022 Interactively
1.1 Minimum System Requirement of Windows Server 2022
1.2 Upgrade or Migrate with Extended Security Updates for legacy Windows Servers
1.3 Creating a Virtual Machine suitable for installing Windows Server 2022
1.4 Desktop Experience installation
2. Common Management Task using Metro UI
2.1 To shutdown or restart the server computer
2.2 To Logoff the current user
2.3 Shortcut keys
3. Server Core
3.1 Purpose of “Server Core”
3.2 Installing Server Core from clean installation
3.3 Configuring a Server Core mode server with PowerShell
3.4 Configuring a Server Core mode server SCONFIG.cmd
3.5 Summary of Server Core and Server with Desktop Experience
4. Implementing On-Premises Active Directory Domain Services (ADDS)
4.1 Requirements of installing and running On-Premises Active Directory Domain Services (ADDS)
4.2 Assigning Static IP Address for a Domain Controller
4.3 Installing ADDS by using ADDS Configuration Wizard
4.4 Verifying ADDS domain configuration
4.5 Configuring a Windows client to join domain
5. IP Address - Internet Protocol version 4 (IPv4)
5.1 Structure (結構) of IP Address
5.2 Concept of Binary Number
5.2.1 First Concept of Binary Number:
5.2.2 Second Concept of Binary Number:
5.3 Network ID and Host ID
5.4 Identifying (辨認) the Network ID
5.4.1 Class A
5.4.2 Class B
5.4.3 Class C
5.4.4 Class D
5.4.5 Class E
5.5 重要事實
5.6 更改IP Address的步驟
5.7 Use of Subnet Mask
5.8 Subnetting (子網路化)
5.8.1 Another Example of Subnetting
5.9 Gateway
5.9.1 Static Route (靜態路線)
5.9.2 Default Gateway (預設閘口)
5.9.3 An Example
5.9.4 設定Default Gateway的步驟
6. Configuring DHCP Server Role
6.1 DHCP Client and Server interaction
6.2 Installing DHCP Server Role
6.3 DHCP Scope
6.4 DHCP Address Exclusion Range
6.5 DHCP Reservation
6.6 Conflict Address Detection
6.7 DHCP Policy Based Assignment (PBA) with User Classes
6.7.1 To create a User Class
6.7.2 To use a User Class
6.8 DHCP Server Network Binding
7. Configuring a Windows Server Router
7.1 Two Router Forms
7.1.1 Hardware Routers
7.1.2 Software Routers
7.2 Routing in Windows Server 2022
7.2.1 To set the default gateway or DC1 and KV1
7.2.2 Enable Routing Service on WS1
7.3 DHCP Relay (接力) Agent (代理人)
7.3.1 Configure a new scope for the network 20.0.0.0 in the DHCP server in DC1
7.3.2 Configure WS1 as a DHCP Relay Agent
7.4 New Client-Side features
7.4.1 New DHCP Client-side features in the Windows 10 April 2018 Update
7.4.2 New DHCP Client-side features in the Windows 10 May 2020 Update
8. Roaming VPN to On-Premises Network
8.1 Configuring VPN
8.2 Deploying VPN Connections using CMAK
8.3 PPTP and L2TP
9. Basic Concept of Storage Virtualization
9.1 Concepts of Storage Pool, Virtual Disk, and Storage Virtualization in Windows Server 2022
9.1.1 Storage Pool
9.1.2 Virtual Disk
9.1.3 Volume
9.2 Configuring a Storage Pool
9.3 Configuring a Virtual Disk
9.3.1 Creating a Simple Virtual Disk
9.3.2 Creating a Mirrored Virtual Disk
9.3.3 Creating a Parity Virtual Disk
9.4 Redundancy of Virtual Disks
9.5 Maintaining Storage Pool
9.6 Repairing a Storage Pool automatically using Hot Spare disks
10. Advanced Concepts of Storage Virtualization
10.1 Introduction to Tiered Storage Pool
10.2 Configuring a Tiered Storage Pool
10.3 Pinning files to specific storage tier
10.4 Storage Tiers Optimization Task
10.5 Dual Parity Non-Tiered Virtual Disks
11. Basic Concepts of Internet SCSI
11.1 Introduction to SCSI and Internet SCSI
11.2 Configuring iSCSI Portal
11.3 Configuring iSCSI Targets
11.4 Configuring iSCSI Initiator
12. Internet Storage Name Service (iSNS)
12.1 Introduction to iSNS
12.2 Installing and Configuring an iSNS Server
12.3 Registering iSCSI Targets
12.4 Configuring iSCSI Initiators to query an iSNS Server
13. NTFS Permissions
13.1 Standard NTFS Permissions on Folders and Files
13.2 Taking Ownership (擁有權) of Folders and Files
13.3 Giving Users the Ability to Take Ownership
13.4 To Take (取得) Ownership
13.5 More About Taking Ownership
14. Share Permissions
14.1 Configuring Share Permissions
14.2 Access-Based Enumeration (ABE)
14.3 Combining Share Permissions and NTFS Permissions
14.4 Access-Denied Assistance
15. File Server Resource Manager
15.1 Introduction to FSRM
15.2 File Server Resource Manager in Quota Management
15.2.1 Quota Templates and standard Quota
15.2.2 Storage Reports Management
15.2.3 Auto Apply Quotas
15.3 File Screening
15.3.1 Create Screening Template
15.3.2 Create File Screens
15.4 File Management Tasks
15.4.1 Creating a File Expiration Task
16. Storage in Azure Cloud
16.1 Creating a Free Azure account
16.1.1 Services included in Azure Free account
16.1.2 Setting up a Free Account
16.2 Storage Account Endpoints
16.2.1 About Require Secure Transfer
16.3 Creating a GPv2 Storage Account
16.4 Introduction to Azure Files
16.5 Data Access Method of Azure Files
16.6 Creating Azure File Share
16.7 Mounting Azure Files
16.8 Azure File Sync
16.8.1 Terminology
16.8.2 Preparing Windows Server
16.8.3 Installing the Azure File Sync Agent
16.8.4 Installing “AzureRM” PowerShell Module
16.8.5 Installing “Az” PowerShell Module
16.8.6 Deploying the Azure File Sync Service
16.8.7 Server Registration
16.8.8 Create a sync group and a cloud endpoint
16.8.9 Creating Server Endpoint
16.9 Cloud Tiering
16.9.1 How Cloud Tiering works
16.9.2 Cloud Tiering Policy
16.9.3 Configuring Cloud Tiering
16.9.4 Forcing Recall of a File or Directory
16.9.5 Unregistering server and removing the Sync Group
17. Windows Server Role
17.1 Domain Controller (DC, 網域控制器)
17.2 Member Server (成員伺服器)
17.3 The Kerberos Authentication Protocol
17.3.1 Understanding Kerberos concepts
17.3.2 Default Kerberos Policy
18. Creating and Managing User Accounts
18.1 To Create Domain User Accounts
18.2 Deleting and Renaming User Accounts
18.2.1 Rename a Domain User Account
18.2.2 Delete a Domain User Account
18.2.3 More about deleted Active Directory Objects
19. Concept of Groups (群組)
19.1 Global Groups (全域群組)
19.2 Local Groups (本機群組)
19.3 General Usage (普遍用法) of a Global Group and a Local Group
19.3.1 Team-up (組合) domain user accounts by a Global Group
19.3.2 Assign (指定) permissions to a Local Group
19.3.3 Add (加入) the Global Group as a member of Local Group
19.4 Some Built-in (內置) Global Groups
19.5 Some Built-in (內置) Local Groups
19.6 Domain Local Groups (網域本機群組)
19.6.1 General Usage (普遍用法) of a Global Group and a Domain Local Group
19.6.2 Some Built-in (內置) Domain Local Groups
19.6.3 Built-in System Groups
19.7 Local User Accounts
19.8 Domain User Accounts
19.9 Built-in (內置) Local User Accounts
19.10 Some Built-in Domain User Accounts
20. Concept of Active Directory
20.1 Logical Structure (企業組織架構)
20.1.1 Domains
20.1.2 Trees (樹)
20.1.3 Forests (森林)
20.1.4 Organizational Unit (OU, 組織單位)
20.2 Physical Structure (企業地理結構)
21. Concepts of Windows Policy (原則)
21.1 Local Computer Policy
21.1.1 Add the Snap-in (加插工具) “Local Computer Policy” to the MMC
21.1.2 Edit a Local Computer Policy Setting
21.2 Site, Domain or OU Policy
21.3 Priority of Windows Policies:
21.4 Important Facts and Rules of Group Policy
21.5 More about Group Policy
21.5.1 Resultant Set of Policy (RSoP) Logging Mode
21.5.2 Resultant Set of Policy (RSoP) Planning Mode
21.5.3 Registry location of computers affected by policies
21.5.4 Disabling Service from domain GPO
21.5.5 Creating Dial-up or VPN connection by Group Policy
21.5.6 Fast Logon Optimization feature – Part I
21.5.7 Fast Logon Optimization feature – Part II
21.6 Refresh Interval for Group Policy
21.7 Group Policy Security Filter
21.8 Group Policy Inheritance
21.9 Using WMI Filters in GPO
21.9.1 Creating a WMI filter
21.9.2 Creating a Group Policy to block removable storage
21.10 Example WMI filters
21.10.1 Targeting based on Operating System
21.10.2 Targeting based on hardware inventory
21.10.3 Targeting based on Chassis Type
21.10.4 Targeting based on “PCSystemType”
21.10.5 Targeting based on amount of disk space and file system type
21.11 Group Policy Restricted Groups
21.12 Group Policy Administrative Templates
21.13 ADMX Central Store
21.13.1 To create the central store:-
21.13.2 Adding Custom ADMX Templates
21.13.3 Benefits of storing ADMX files in Central Store (SYSVOL)
21.13.4 To add French support of Office Word 2016 related group policies:-
21.14 Administering Group Policy Objects by using PowerShell
21.14.1 Get-GPO
21.14.2 Get-GPOReport
21.14.3 Get-GPInheritance
21.14.4 New-GPLink
21.14.5 Set-GPLink
21.14.6 Remove-GPLink
21.14.7 Get-GPPermissions
21.14.8 Backup-GPO
21.14.9 Remove-GPO
21.14.10 Import-GPO
21.15 Software Deployment with Group Policy Object
21.15.1 Publishing (出版) Software to Users
21.15.2 Assigning (指定) Software to Users
21.15.3 Assigning Software to Computers
21.15.4 Remote Group Policy Refresh
21.16 Group Policy Startup Script
21.17 Group Policy Scripts Processing
21.18 Group Policy Slow-link detection
21.18.1 To simulate a fast-link situation
21.18.2 To simulate a slow-link situation
21.18.3 To disable “Group Policy Slow Link Detection”
21.18.4 To simulate a slow-link situation when Group Policy Slow Link Detection is Disabled
22. Domain Functional Level (DFL)
22.1 Understanding AD DS Domain Function Levels
22.2 Supported Domain Functional Level and Features bv Windows Server 2022
22.3 Group Types of Active Directory
22.3.1 Security Group
22.3.2 Distribution Group
22.4 Scopes (範圍) of Security Group
22.4.1 Domain Local Group
22.4.2 Global Group
22.4.3 Universal Group (通用群組)
22.5 Common Usage (普遍用法) of Global Group, Universal Group and Local Group
22.6 Creation of a Group
22.7 Raise Domain Functional Level
22.8 Rollback Options of Domain Functional Level (Optional Knowledge)
22.9 Using Fine-Grained Password and Lockout Policy
22.10 Preparation
22.11 Creating Password Setting Objects by using ADSI Editor and ADAC
22.12 Apply PSOs to Users or Global Groups
22.12.1 Viewing Resultant PSO
22.12.2 The logic behind precedence: calculating RSOP
22.12.3 Scenario I: Using PSO after Upgrading to Windows Server 2022
22.12.4 Scenario II: Migrating to Windows Server 2022 with PSO support
23. Forest Functional Level
23.1 Forest Functional Levels available in Windows Server
23.2 Guidelines for raising Forest Functional Level
24. Active Directory Recycle Bin
24.1 About deleted Active Directory Objects
24.2 Overview of Restoring Active Directory objects by Recycle Bin
24.3 Enabling the Active Directory Recycle Bin
24.4 LDAP Names
24.5 Restoring Active Directory Objects
24.6 More about restoring multiple Active Directory Objects
25. Additional Domain Controllers
25.1 Installing Additional Domain Controllers by Network
25.2 LDAP Names
25.3 Effects on Active Directory with additional domain controllers
25.3.1 Computer account of DC2
25.3.2 Site location of DC2
25.3.3 Service Resource Records updated
26. DHCP High Availability
26.1 Multiple DHCP Servers on the Same Network
26.1.1 To Install and Authorize DHCP Server on DC2
26.1.2 Using the Split Scope Wizard
26.2 DHCP Failover
26.3 About DHCP Load Sharing mode
27. Global Catalog and FSMO Roles
27.1 Introduction to Global Catalog and FSMO Roles
27.2 Global Catalog (通用類別目錄)
27.3 Compacting Active Directory Database
27.4 Schema Master – Per Forest
27.4.1 To display current Schema Master Role
27.4.2 To safely transfer the Schema Master Role to DC2
27.4.3 To Seize (強奪) transfer the Schema Master Role on DC1
27.4.4 To extend Active Directory Schema
27.4.5 To disable an Active Directory Schema
27.5 Domain Naming Master – Per forest
27.5.1 To display current Domain Naming Master of your forest
27.5.2 To safely transfer Domain Naming Master role to DC2
27.5.3 To seize Domain Naming Master role at DC1
27.6 PDC Emulator– Per Domain
27.6.1 Configuring Windows Time Service on PDC Emulator
27.7 Relative ID Master – Per Domain
27.7.1 To display current RID Master of your forest
27.8 Infrastructure Master – Per Domain
27.9 Active Directory Replication Status Tool
28. Azure Active Directory (AAD)
28.1 Azure AD Administrator Roles
28.2 Users and Licenses of Azure Active Directory
28.3 Terminology of Azure Active Directory
28.4 Azure Active Directory Custom Domain names
28.5 Creating Azure AD User account
28.6 Managing User Profile Information
28.7 Resetting Azure Active Directory User Password
28.8 Configure Access with Azure Active Directory Groups
28.9 Dynamic Group
28.10 Differences between Azure RBAC roles and Azure AD administrator roles
28.11 Set up directory synchronization
28.11.1 Principal of Password Hash Synchronization
28.12 Monitoring AD Connect Synchronization Health
28.12.1 Azure AD Connect Sync Insight
28.12.2 Sync Latency
28.12.3 Sync Object Changes
29. Windows Admin Center
29.1 Overview of Windows Admin Center
29.2 Deploying Windows Admin Center
29.3 Configuring Windows Admin Center
29.4 Enabling Windows Admin Center Single-Sign On (SSO)
29.5 Deploying Extensions to Windows Admin Center
30. NIC Teaming
30.1 Introduction to NIC Teaming
30.2 Configuring NIC Teaming
30.3 Configuring LACP
31. Windows Containers
31.1 Introduction to Windows Containers
31.2 Fundamental Concepts of Windows Containers
31.2.1 The Microsoft container ecosystem
31.2.2 Container Host
31.2.3 Container Image
31.2.4 Sandbox
31.2.5 Container OS Image:
31.2.6 Container Repository
31.3 Windows Container Types
31.3.1 Windows Server Containers
31.3.2 Hyper-V Container
31.4 Introduction to Docker
31.5 Containers for Developers
31.6 Containers for IT Professionals
31.7 Configuring Windows Container Host
31.8 Deploying a container
31.9 Building Container Images
31.9.1 Manually creating container image
31.10 Hyper-V Containers
31.11 A Special Reminder on Hyper-V Container Host
31.12 More about Hyper-V isolation
31.13 Container Networking Concepts
32. Azure Container Instances (ACI)
32.1 Introduction to ACI
32.2 Creating Azure Container Instance
32.3 Viewing Container Logs
32.4 Quota and Limits of Azure Container Instances
33. Azure Container Registry (ACR)
33.1 Introduction to Azure Container Registry, Repository and Images
33.1.1 About Container Registry
33.1.2 About Repository
33.1.3 About Container Image
33.2 Use cases and Key features of Azure Container Registry
33.3 Creating a Private Container Registry
33.4 Pull, Build, Push, Run a container image using Azure Container Registry Tasks
33.5 Azure Container Registry Roles and Permissions
34. High Availability Features
34.1 Failover Clusters
34.1.1 Quorum Configuration in Windows Server
34.1.2 Two-node file server cluster
34.1.3 Configure Possible Owners
34.1.4 Failback
34.2 Scale-Out File Server for Application Data
34.2.1 Introduction to Scale-Out File Server
34.2.2 Deploying a Scale-Out File Server
34.3 Configuring Hyper-V to use Scale-Out File Server (Optional Knowledge)
34.4 The SMB Witness protocol (Optional knowledge)
34.5 Managing a Failover Cluster with Windows Admin Center
35. Configuring ADDS Forest
35.1 Additional Domains in existing Forest
35.2 Configuring a new domain tree to join existing forest
35.2.1 Creating new Domain Tree to join existing Forest on DCA
35.2.2 Check the Trust relationship
35.3 Conditional DNS Forwarding
35.3.1 Enable Conditional forwarding of xyz.com in systematic.com’s DNS Server
35.3.2 Enable Conditional forwarding of systematic.com in xyz.com’s DNS Server
35.4 Enabling Global Catalog (GC) for xyz.com
35.4.1 Enabling GC on dca.xyz.com
35.4.2 Adding DNS Service Location (SRV) Record for Global Catalog Server
35.5 An Example of Domain-Wide authentication and Resource assessment
35.6 Assigning Permissions in a multi-domain environment
35.7 Active Directory Migration Tool
35.7.1 Installing ADMT and SQL Server Express
35.7.2 Migrating Domain User Account
35.8 Deploying Child Domain
35.8.1 Creating DNS Delegation for domain “money.xyz.com”
35.8.2 Deploying domain controller for a child domain
36. Managing ADDS Trusts
36.1 Types of Trust within a Forest (Intra-Forest)
36.2 Types of Inter-Forest Trust (Inter-Forest)
36.3 Creating Forest Trust
36.3.1 Background
36.3.2 Creating a Two-Way Transitive Forest Trust
36.4 Updating UPN Suffixes for Forest Trust
36.5 Selective Authentication
36.5.1 事前驗證
36.5.2 Deploying Selective Authentication
36.5.3 Granting “Allowed-to-Authenticate” permission on KV1
37. On-Premise and Internet DNS
37.1 The Domain Name Space
37.2 Types of Windows DNS Zones
37.3 Active Directory Integrated Zone
37.3.1 Zone data storage of Active Directory Integrated Zone
37.3.2 Zone Replication Scope
37.3.3 Using Application Directory Partition
37.4 Standard Primary Zone
37.5 Standard Secondary Zone
37.6 Three Methods to Implement a DNS Zone
37.6.1 To Install One More DNS Server on WS2 and managed by DC1
37.6.2 To Create systematic.com Standard Secondary Zone for WS2 DNS Server
37.6.3 Configure DC1 to allow zone transfer to WS2 DNS Server
37.7 Forward Lookup Zone and Host (A) Records
37.8 Reverse Lookup Zone and Pointer (PTR) Records
37.8.1 To Create a Reverse Lookup Zone
37.8.2 To Create a Pointer (PTR) Record
37.9 Forward Lookup Zone and Mail Exchanger (MX) Records
37.10 Name Server (NS) Record and the Name Servers Tab
37.11 More about Zone Transfer from Primary to Standard Secondary
37.12 DNS Sub-domains
37.12.1 Creating a DNS Sub-domain By Using “New Domain”
37.12.2 Creating a DNS Sub-domain By Using “New Delegation”
37.12.3 Creating a DNS Sub-domain By Using “Stub Zone”
37.13 Background zone loading
37.14 Global Names Zone
37.14.1 To create a Global Names Zone (GNZ)
37.14.2 Deploying GlobalNames zone for Multiple forest
37.15 Three Tiers (三重) of Caching (緩衝)
37.15.1 1st Tier – Client Side Caching
37.15.2 2nd Tier – Queries through an Cache (中途的) DNS server
37.15.3 3nd Tier – Memory Caching on Authoritative Primary or Secondary Servers
37.16 Forwarders
37.16.1 Server-level Forwarder
37.16.2 Conditional Forwarder
37.16.3 Configuring Conditional Forwarders
37.16.4 Storing Conditional Forwarder in Active Directory
37.17 Root Zone, Root Hints
37.17.1 Creating Root Zone
37.17.2 Deleting Root Zone
AZ-801 Configuring Windows Server Hybrid Advanced Services (36 hrs)
1. Advanced DNS Server configuration
1.1 Round Robin Mechanism (輪流運作的技巧)
1.2 Enable Netmask Ordering
1.3 More about Zone Transfer: AXFR and IXFR
1.4 BIND Secondaries
1.5 DNS Debug Logging
1.6 Removing out-dated DNS records
1.7 Exporting Zone Files
1.8 Securing DNS resource records
1.9 Dynamic Update
1.9.1 Situation (處境) when “Dynamic updates” is set to “Nonsecure and secure”
1.9.2 Situation (處境) when “Dynamic updates” is set to “Secure Only”
1.10 Restricting DNS Server interface binding
1.11 Internet Domain Name Registration
1.11.1 To register a domain
1.11.2 To maintain a domain
2. DNS Client side configuration
2.1 Configuring DNS client statically
2.2 Configuring DNS client dynamically
2.3 Configuring DNS client by NRPT policy
3. DNS Security Extensions
3.1 Overview of DNSSEC
3.2 Threats of DNS Protocol
3.3 Principal of DNS Security Extension
3.3.1 Digital Signatures
3.3.2 Zone Signing
3.3.3 Authenticated Denial of Existence
3.3.4 Trust Anchors
3.3.5 DNSSEC key management
3.3.6 DNSSEC-aware DNS Clients
3.3.7 NRPT Policy for DNSSEC Validation
3.4 A DNSSEC Test Lab scenario
3.4.1 Create the zone “fabrikam.com”
3.4.2 Configure the cache DNS server WS2
3.4.3 Reconfigure DNS Client to use Cache DNS Server
3.5 Configuring and testing DNSSEC
3.5.1 Query unsigned zones without DNSSEC validation requirement
3.5.2 Signing a zone by DNSSEC
3.5.3 To distribute Trust Anchor Manually
3.5.4 Querying a Signed-Zone without Validation requirement
3.5.5 Configuring DNS Client to perform DNSSEC validation
3.5.6 Querying a Signed-zone with Validation required
3.5.7 Situation when Validation Failed
3.5.8 Situation when the attacker uses a Fake signature
3.6 More about using DNSSEC for Public Internet Domains
4. Windows Server Compute and Virtualization services
4.1 Microsoft Hyper-V Server and Windows Server Hyper-V role
4.2 Hyper-V General Requirements
4.2.1 CPU and BIOS/UEFI Firmware
4.2.2 More about Logical Processor and Virtual Processor
4.2.3 Memory
4.2.4 Network/NIC Requirements
4.2.5 Storage
4.3 Installing Hyper-V Role Service on Windows Server 2022
4.4 Creating a Virtual Machine and Installing a Guest OS
4.5 Installing and Configuring Windows Hyper-V Server
4.6 Configuring Hyper-V Server to accept Remote Management
4.7 Managing Hyper-V Server from a remote location
5. Configure Hyper-V Settings and Virtual Networks
5.1 Configuring VHD Storage location
5.2 Upgrading Virtual Machine Configuration Version
5.3 Checkpoint (Snapshot) Location
5.3.1 Standard Checkpoint
5.3.2 Production Checkpoint
5.4 Hot add and Hot removal of Virtual hardware
5.5 Nested Virtualization
5.6 Host Resource Protection
5.7 Windows PowerShell Direct
5.8 Managing Multiple Virtual Machines
5.8.1 Creating VM collections
5.8.2 Creating Management Collections
5.9 Configuring the Virtual Network
5.9.1 Virtual Switch Manager
5.9.2 Virtual Network Connection Type
5.9.3 External virtual networks
5.10 Guest Network Load Balancing
5.10.1 Installing Network Interface Driver on Microsoft Hyper-V Server
5.10.2 Connecting a the Hyper-V Host to a VLAN
5.10.3 Connecting a the Hyper-V Child Partition to a VLAN
5.11 Single Root I/O Virtualization
6. Shared Nothing Live Migration
6.1 Concepts of Live Migration
6.2 Configuring Live Migration in a Shared Nothing/Non-Clustered environment
6.3 Performing Live Migration of virtual machine in a Shared Nothing environment
6.4 More about Processor Compatibility Mode
7. Hyper-V Replica Server
7.1 Introduction to Hyper-V Replica
7.2 Configuring Hyper-V Replica
7.3 Testing Failover
7.4 Performing a Planned Failover
7.5 Performing a Un-planned Failover
8. Generation 2 Virtual Machines
8.1 Generation 2 Virtual Machine in Hyper-V
8.1.1 To create a Generation 2 virtual machine:
8.2 Storage QoS of Hyper-V
8.2.1 Key benefits of Storage QoS of Hyper-V virtual machines
8.2.2 To configure a virtual hard disk (or virtual machine) for Storage QoS
8.3 Enhanced Session Mode
8.3.1 Overview of Enhanced Session Mode
8.3.2 Practical application of Enhanced Session Mode
8.3.3 To enable Enhanced Session Mode
8.4 Automatic Virtual Machine Activation
8.4.1 Introduction and Implementing Automatic Virtual Machine Activation
8.5 Virtual Disk Online Resizing
8.6 Non-Uniform Memory Architecture (NUMA)
8.7 Resource Metering (計量)
8.7.1 Overview of Hyper-V Resource Metering
8.7.2 Enabling and Using Resource Metering
8.7.3 Using Virtual Network Adapter ACL
8.8 Hyper-V Port Mirroring
8.9 Using ReFS version 2 with Hyper-V
9. Hyper-V Failover Clustering
9.1 Deploying a Hyper-V Failover Cluster
9.2 Cluster Shared Volume
9.3 Cluster Shared Volumes (CSV) Cache
9.4 Deploying a Highly Available Virtual Machine in Hyper-V Cluster
9.5 Testing a Planned Failover by Live Migration
9.6 Virtual Machine Drain on Shutdown
9.7 Live Migration Settings and RDMA
9.7.1 Live Migration Settings
9.7.2 RDMA (Remote Direct Memory Access)
9.8 Virtual Machine Network Health Protection
9.9 Virtual Machine Monitoring
9.10 Hyper-V Replica Broker
9.10.1 Introduction to Hyper-V Broker role and usage scenario
9.11 Hyper-V Virtual Machine Load Balancing
9.12 Configuring RDMA Adapter and Converged Ethernet
9.12.1 Data Center Bridging for RDMA
9.12.2 Creating a Hyper-V Virtual Switch with an RDMA Capable adapter
9.13 Hyper-V Switch Embedded Teaming (SET)
9.13.1 Introduction to Hyper-V Server Switch Embedded Teaming
9.13.2 Switch Embedded Teaming Compatibility with existing Windows Server technologies
9.13.3 Creating a SET Team in Hyper-V
9.13.4 SET Modes and Balancing Algorithms
10. Creating and Managing Azure Virtual Machines
10.1 Benefits and Challenges using N-Tier Architecture
10.2 N-Tier architecture with Azure Compute Virtual Machines
10.2.1 To Implement N-Tier Virtual Machine based Architecture
10.3 Enabling Auto-shutdown for VM
10.4 Configuring and Managing additional data disk for Azure Virtual Machines
10.5 Configure Azure Disk Encryption
10.5.1 Azure Disk Encryption Workflow
10.5.2 Azure Disk Decryption Workflow
10.5.3 Azure Disk Encryption Prerequisites
10.5.4 Supported VM Sizes
10.5.5 Virtual Networking
10.5.6 Key Vault Access Policy
10.5.7 Enable encryption on existing or running IaaS Windows VMs
10.6 Resizing Virtual Machines
10.6.1 To Resize a virtual machine which is available in the current cluster
10.6.2 Resizing a Virtual Machine to support Ultra Disk
10.6.3 Resize Resource Manager (ARM) virtual machine to size not available in current hardware cluster
10.7 Hot Patching
10.7.1 How hotpatching works
10.7.2 Deploy a new Azure VM with hotpatch for Windows Server enabled
10.8 SMB over QUIC
10.8.1 SMB protocol
10.8.2 QUIC protocol
10.8.3 Deploy SMB over QUIC
10.9 SMB over QUIC with Automanage
11. Cross Premises and Hybrid Connectivity
11.1 Introduction to VNet Peering
11.1.1 Benefits of VNet Peering
11.1.2 Connectivity
11.1.3 Service chaining
11.1.4 Gateways and on-premises connectivity
11.2 Configuring Global VNet Peering
11.3 Options for connecting additional virtual networks
11.4 Point-to-Site VPN and Certification based authentication
11.4.1 Generating a Client Authentication certificate
11.4.2 Exporting the Root Certificate in BASE64 public key .cer format
11.4.3 Configuring VPN Client Address Pool and Tunnel Type
11.4.4 Uploading trusted Root Certificate
11.4.5 Generate VPN Client packages
11.5 Configuring Azure Site to Site (S2S) VPN
11.5.1 Configuring Site-to-Site Connections in Azure VPN Gateway
11.5.2 Configuring On-Premises VPN device
11.5.3 Verifying Connectivity
11.6 Azure Virtual Network Adapter
11.6.1 Register a WAC Gateway with Azure Cloud
11.6.2 Add an Azure Network Adapter to a server
11.7 Microsoft Defender for Cloud
11.7.1 Set up Microsoft Defender for Cloud
11.7.2 Microsoft Defender for Servers
11.7.3 Onboarding your machines to threat and vulnerability management
11.7.4 Just-In-Time (JIT) VM access
11.7.5 Adaptive Application Control
11.7.6 Connect your non-Azure machines to Microsoft Defender for Cloud
12. Microsoft Defender for Identity
12.1 Introduction to MDI/Azure ATP
12.1.1 Monitor and analyze user behavior and activities
12.1.2 Protect user identities and reduce the attack surface
12.1.3 Identify suspicious activities and advanced attacks across the cyber-attack kill-chain
12.2 Microsoft Defender for Identity architecture
12.2.1 Defender for Identity components
12.2.2 Defender for Identity portal
12.2.3 Defender for Identity sensor
12.2.4 Requirements
12.3 Creating a Defender for Identity Instance
12.4 Connect to your On-Premises AD Forest
12.5 Downloading and Installing the Sensor setup package
12.6 Configure Data Steering in MDI Sensor
12.7 About Microsoft Advanced Threat Analytics (ATA)
12.8 Security Posture Assessments with Microsoft Defender for Identity
13. Data Deduplication
13.1 Introduction to Data Deduplication in Windows Server 2022
13.2 Installing and Configuring Data Deduplication
13.3 Data Deduplication enhancements in Window Server
13.3.1 Support for large volumes
13.3.2 Shortened Deduplication process
13.3.3 Support for large files
13.4 Additional Interoperability considerations of using Data Deduplication
13.4.1 DFS Replication
13.4.2 FSRM Quotas
14. On-Premises Performance Monitoring
14.1 Reliability Analysis Component (RAC)
14.2 Data Collector Set
14.3 Performance Counter Alert
14.4 Event Trace Sessions
15. Azure Recovery Services Vault
15.1 Introduction to Recovery Services Vault
15.2 Creating a Recovery Services Vault
15.3 Back up Windows to Azure
15.3.1 Configuring the Vault for backing up On-Premises Windows
15.3.2 Installing Agent and Registering On-Premises Server
15.3.3 Create the backup policy
15.3.4 Network throttling
15.3.5 Restoring files from Azure Recovery Services Vault
15.4 Back up an Azure Virtual Machine
15.4.1 Preparation to backup Azure Virtual Machine
15.4.2 Network Connectivity from VM Guest Agent to Azure public IP addresses
15.4.3 Back up the Azure VM using Azure Backup service
15.5 Upgrading Azure VM Backup stack V2 (Optional knowledge)
15.6 More about Site-to-Site recovery by using Azure Site Recovery
15.6.1 Introduction to Azure Site Recovery services
15.6.2 Migrating On-premises Hyper-V Virtual Machine to Azure
15.6.3 Disaster Recovery Drill
15.6.4 Completing the Migration of Hyper-V Virtual Machine
15.6.5 After Migration
16. Azure Migrate Appliance
16.1 Introduction to Azure Migrate
16.2 Creating a Migration Project
16.3 Deploying Azure Migrate appliance with VHD template for Hyper-V
16.3.1 Generate the project key
16.3.2 Download the VHD template
16.3.3 Creating the appliance
16.3.4 Configuring the Azure Migrate virtual appliance
16.3.5 Set up prerequisites and register the appliance
16.3.6 Starting Continuous Discovery of Hyper-V infrastructure
16.4 Assess Hyper-V VMs for migration to Azure
16.5 Migrate Hyper-V VMs to Azure
16.6 Running a Test Migration
16.7 Migrating to Azure Virtual Machines
16.8 Completing the migration
16.9 Post-migration best practices
17. Protecting and Securing Windows Credentials
17.1 Attacks to Windows Credential Store
17.2 Requirements of Credential Guard
17.3 Configuring Credential Guard
17.4 Preventing NTLM authentication protocol
18. Just Enough Administration (JEA)
18.1 Overview of Just Enough Administration
18.1.1 JEA Objectives
18.1.2 JEA reduces risk by limiting administrator exposure
18.1.3 JEA Working Principal
18.1.4 Benefits of JEA
18.1.5 JEA Deployment Prerequisites
18.2 Creating a JEA Role Capability File
18.3 Convert Role Capability File as PowerShell Module
18.4 Creating a JEA Session Configuration File
18.5 Creating a JEA Endpoint
18.6 Connecting to JEA Endpoint
19. Azure ARC
19.1 Introduction to Hybrid Infrastructure Management with Azure ARC
19.2 Azure ARC Enabled Servers
19.3 Onboarding Azure ARC Enabled Servers
19.3.1 Generate installation script
19.3.2 Install the agent using the script
19.4 Onboarding ARC Enabled Servers at Scale
19.5 Onboarding ARC Enabled Servers to Microsoft Sentinel
19.6 Detect threats using Microsoft Sentinel
19.7 Moreover Automated Response to Threats
 付款。
付款。