(在家觀看 = 0%,在校觀看 = 100%)
100% 在校觀看日期及時間:
自由選擇,點選以下地區觀看辦公時間及位置
課時: 18 小時
享用時期: 9 星期。進度由您控制,可快可慢。
課堂錄影導師:Franco
在校免費試睇:首 1 小時,請致電以上地點與本中心職員預約。
本課程提供在校免費重睇及導師解答服務。
(在家觀看 = 100%,在校觀看 = 0%)
100% 在家觀看日期及時間:
每天 24 小時全天候不限次數地觀看
課時: 18 小時
享用時期: 9 星期。進度由您控制,可快可慢。
課堂錄影導師:Franco
在校免費試睇:首 1 小時,請致電以上地點與本中心職員預約。
本課程提供導師解答服務。
隨著網絡技術日益普及,大家都開始擔心網絡和資訊保安的問題。故此各大網絡硬件和軟件製造商紛紛推出多個保安產品以提升企業網絡保安水平。 Check Point 便是當中的翹楚。 Check Point 是著名的防火牆 (Firewall) 及虛擬私人網絡 (VPN) 的生產商,其產品遍佈全球。故此掌握 Check Point 技術乃是大勢所趨。
為證明您能掌握各項 Check Point 技術, Check Point 推出了一系列的認證。而最為普遍的有:
- CCSA R81 (Check Point Certified Security Administrator R81)
- CCSE R81 (Check Point Certified Security Expert R81)
CCSA R81 是 Check Point 入門級的認證,考過 CCSA R81 後,同學便可以考取更高級的 CCSE R81 認證。
本課程專為同學考取 CCSA R81 國際認可證書而設,導師將在課堂上使用 Check Point R81 示範和教授各項 Check Point 技術。修畢課程後,便可參加考試 156-215.81.20 (Check Point Security Administration R81),合格後便可成為 CCSA R81!
| 課程名稱: |
Check Point CCSA R81 國際認可證書課程 - 簡稱:Check Point CCSA Training Course (R81) |
| 課程時數: | 合共 18 小時 |
| 適合人士: | 對防火牆及虛擬私人網絡技術有興趣的人士 |
| 授課語言: | 以廣東話為主,輔以英語 |
| 課程筆記: | 本中心導師親自編寫英文筆記 |
| 1. Franco 親自教授: | Franco 善於控制學習節奏,深入淺出,令學員在輕鬆的氣氛下掌握知識。 |
| 2. Franco 親自編寫筆記: | Franco 親自編寫筆記,絕對適合考試及實際操作 Check Point 器材之用,令你無須「死鋤」如字典般厚及不適合香港讀書格調的書本。 |
| 3. 理論與實習並重: | Franco 的筆記不會紙上談兵,筆記內有大量商業實習。 |
| 4. 提供模擬考試題目: | 本中心為學員提供模擬考試題目,每條考試題目均附有標準答案。 |
| 5. 提供 Check Point R81 (15-day Plug n Play license) 軟件: | 提供 Check Point R81 (15-day Plug n Play license) 軟件,令學員可以自行安裝 Check Point R81。 |
| 6. 免費重讀: | 傳統課堂學員可於課程結束後三個月內免費重看課堂錄影。 |
只要你於下列科目取得合格成績,便可獲 Check Point 頒發 CCSA R81 國際認可證書:
| 考試編號 | 科目名稱 |
| 156-215.81.20 | Check Point Certified Security Administrator R81 |
本中心為 Check Point 指定的 CCSA R81 考試試場,報考時請致電本中心,登記欲報考之科目考試編號、考試日期及時間 ( 最快可即日報考 ) 。臨考試前要出示身份證及繳付考試費 HK$2,460。 臨考試前要繳付考試費 HK$2,460,及必須出示下列兩項有效之身份證明文件,否則考生不可進行考試,而已繳付之考試費亦不會退回: |
|
課程名稱:Check Point CCSA R81 國際認可證書課程 - 簡稱:Check Point CCSA Training Course (R81) |
第 1 部份:Check Point Software Architecture
- 教授 Gaia 在 Check Point solutions 的功能和角色,安裝及設定 [GUI (Graphical User Interface) + CLI (Command Line Interface)]
- 教授 Security Management Server 在 Check Point solutions 的功能和角色,安裝及設定 Security Management Server。
- 教授 Security Gateway 在 Check Point solutions 的功能和角色,安裝及設定 Security Gateway。
- 教授 Smart Console 在 Check Point solutions 的功能和角色,安裝及設定 Smart Console。
- 教授 Distributed deployment。
- 其他相關知識包括 SIC、folder / file architecture 等等。
第 2 部份:Firewall
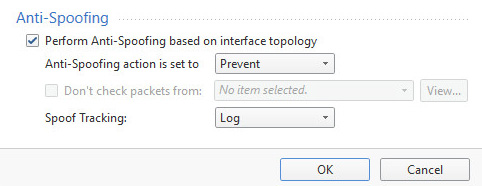
- 教授 Anti-spoofing 概念及設定。
- 教授基本 Packet filtering。

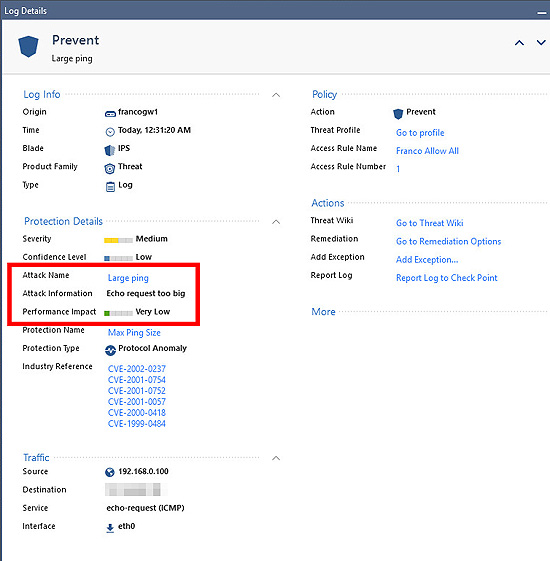
- 教授 Threat Prevention (IPS, Intrusion Prevention System),並以過濾過大的 ping packet 作示範。
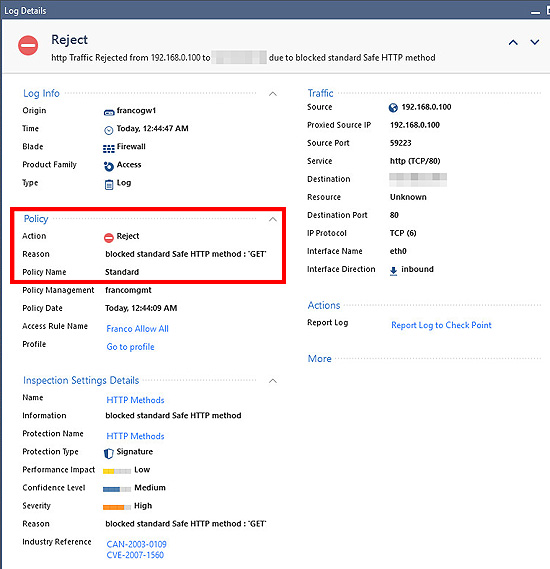
- 教授 Application Inspection,並以過濾 HTTP GET 作示範。
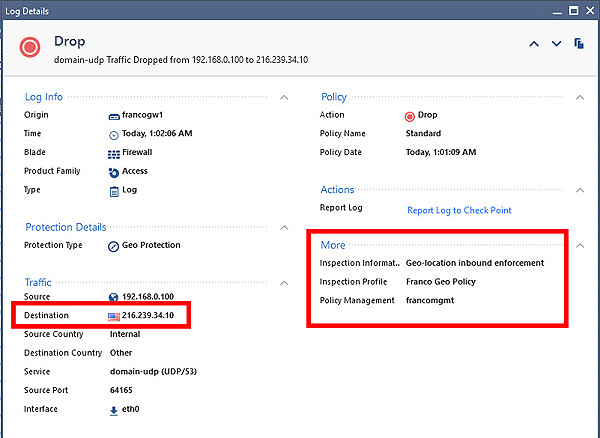
- 教授 Geo Protection,並以過濾外國的 packets 作示範。
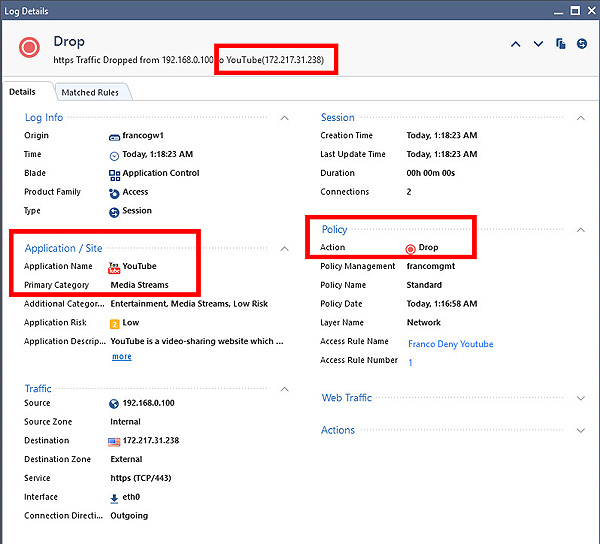
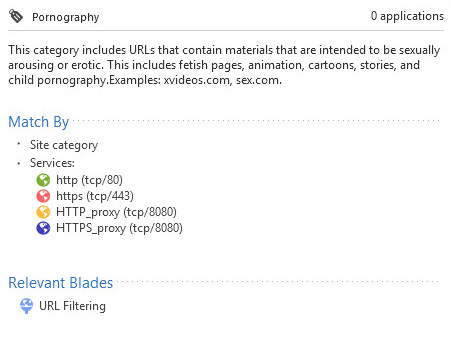
- 教授 Application Control 和 URL filtering,並以過濾 YouTube / Facebook 等網站作示範。
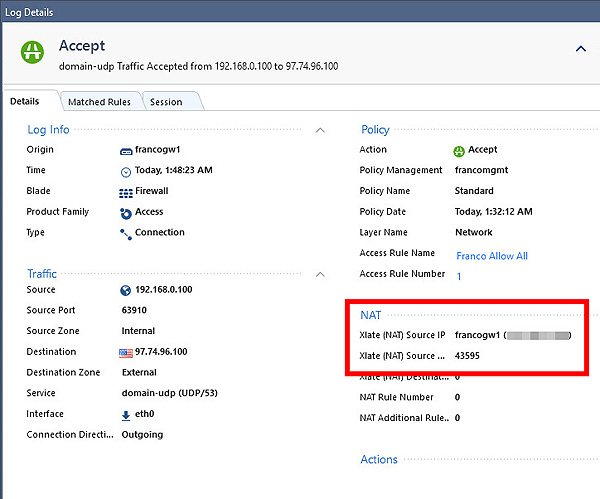
- 教授 NAT 並作 dynamic 和 static NAT 的示範。
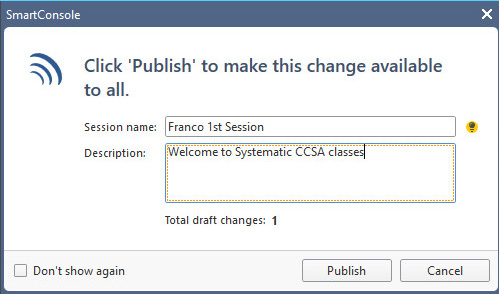
- 教授其他 Firewall 相關知識,例如 implied rules, policy management, sessions, publish 等概念。
第 3 部份:Identity awareness, monitor and log management
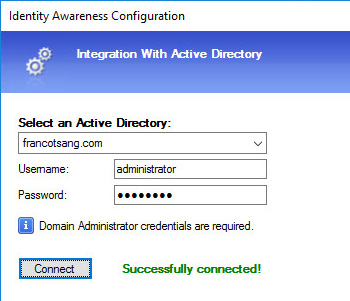
- 教授 Identity awareness 理論並教授如何將 Security Gateway連接 Microsoft Active Directory。
- 教授從 Check Point 產品內 browse Active Directory 結構。
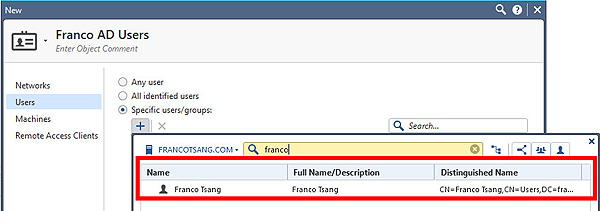
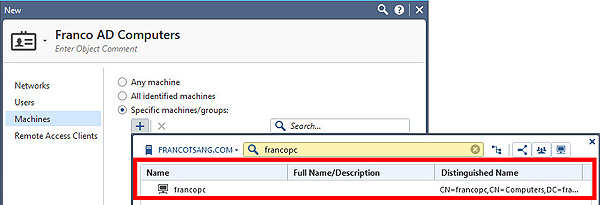
- 在記錄內顯示 Active Directory 的 computers 和 users。
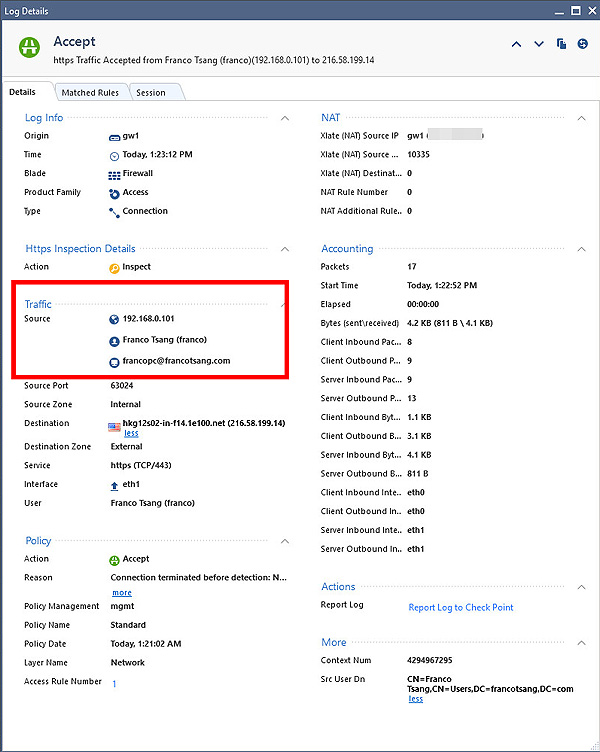
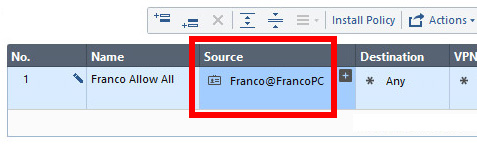
- 在 Rule 上加上 Active Directory 的 users / machines。
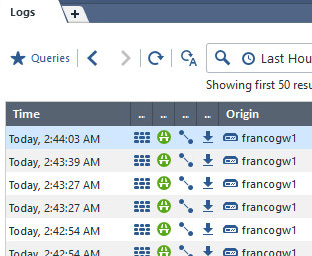
- 教授 Check Point 的 monitor 和 logs 機制。
- 教授 Views 並顯示 Views。
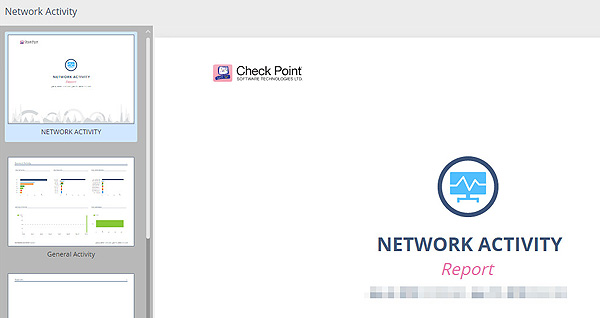
- 教授如何產生 reports。
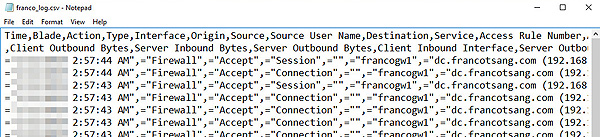
- 教授將記錄 export 為 csv 以便其他程式使用。
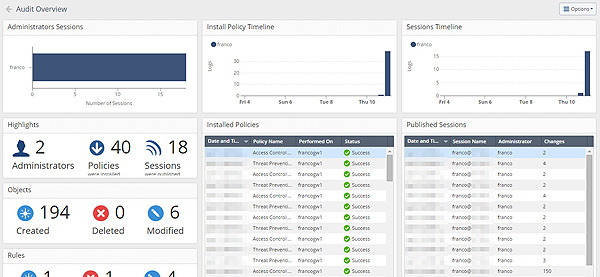
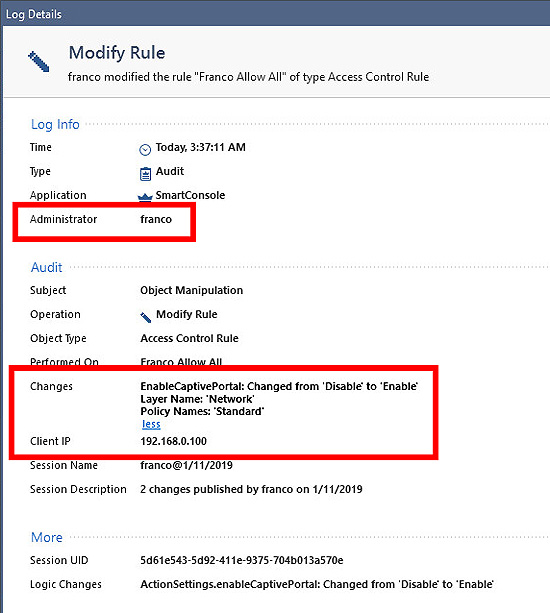
- 教授將記錄 security administrator 的活動,例如修改 Firewall rules。
- 教授了解 Check Point Security Management Server 及 Security Gateway 的情況。
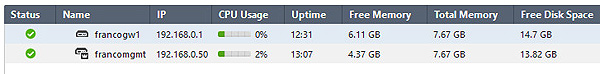
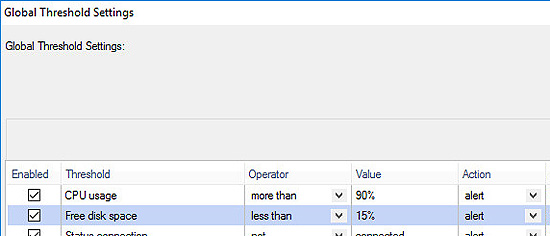
- 教授如何處理 CPU 太高或 disk space 過少等問題。
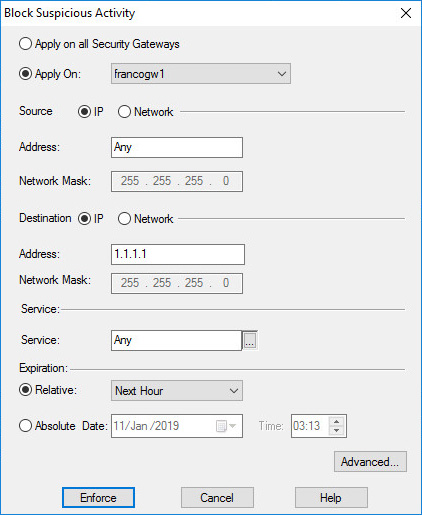
- 教授 Block Suspicious Activity 的概念,應用時機並實踐出來。
- 教授其他 Identity awareness, monitor and log management 知識。
第 4 部份:VPN
- 教授一般的 IPSec VPN 理論 (非常重要)。
- 教授針對 Check Point的 IPSec VPN 概念。
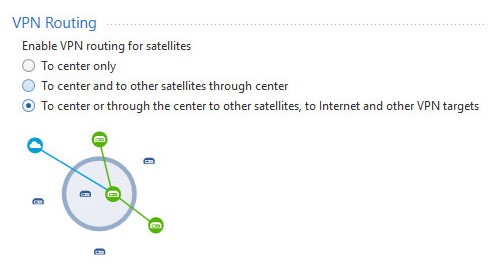
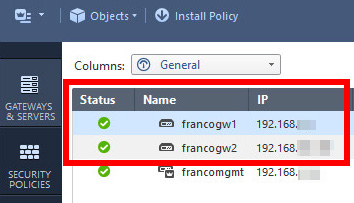
- 教授同時管理多個 Security Gateways 以準備設定 VPN。
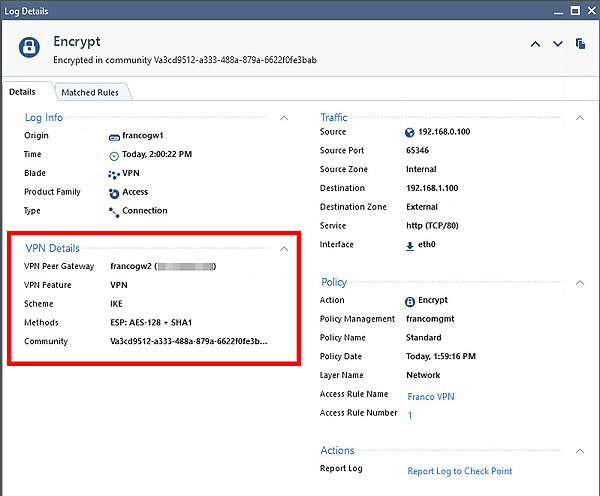
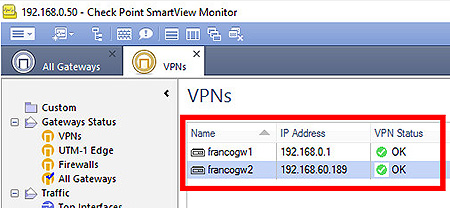
- 教授建立和監察 VPN。
第 5 部份:Miscellaneous
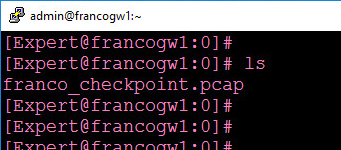
- 教授在 Security Gateway 內 capture Wireshark 以便學習及解決問題。
- Administrations and disaster recovery concepts (e.g. Backup, restoration, account management, etc.)。
- 其他話題。
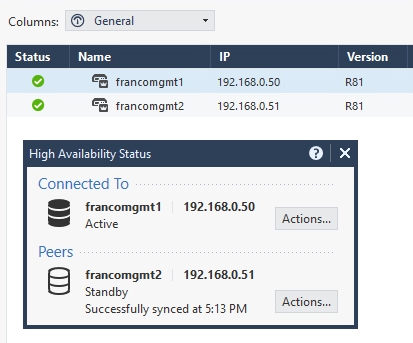
- 教授 Management High Availability。
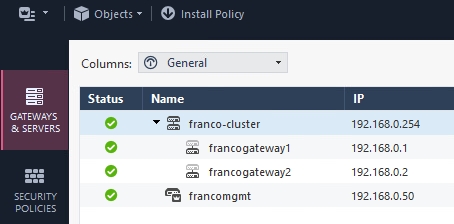
- 教授 ClusterXL。
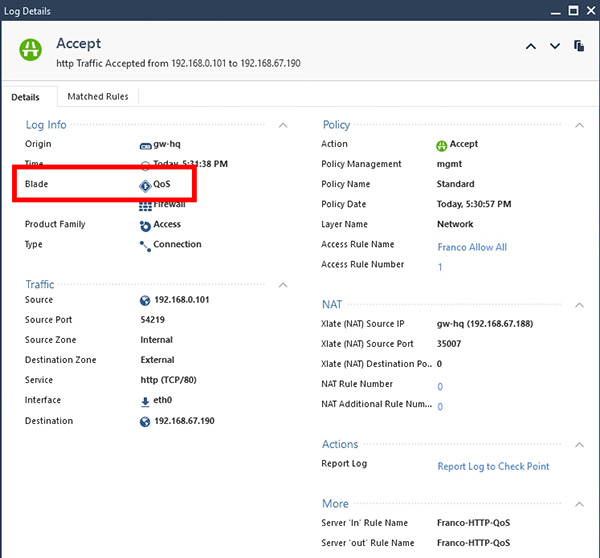
- 教授 QoS (Quality of service)。
The course content above may change at any time without notice in order to better reflect the content of the examination.
1 Check Point Gaia
1.1 Introduction
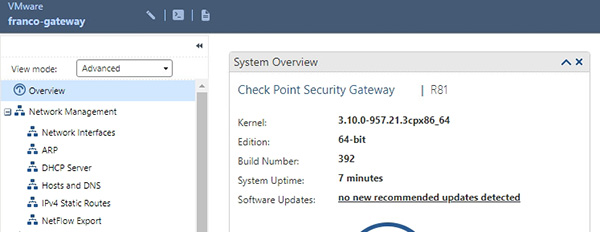
1.2 Gaia GUI
2 Check Point Architectures
2.1 Overall Concepts of Check Point Architectures
2.1.1 Security Management Server
2.1.2 Security Gateway
2.1.3 SmartConsole
2.2 R81
2.3 Quick tour of SmartConsole
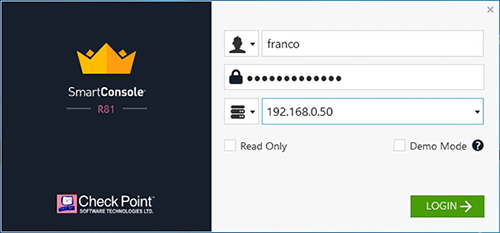
2.3.1 Log in
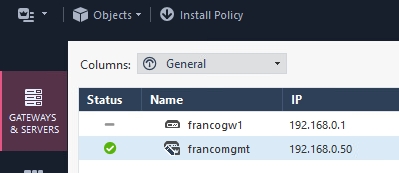
2.3.2 Gateways & Servers
2.3.3 Security Policies
2.3.3.1 Security Policies Access Control
2.3.3.2 Security Policies Threat Prevention
2.3.4 Logs & Monitor
2.3.5 Manage & Settings
2.3.6 The main SmartConsole Menu
2.3.7 The Objects Menu
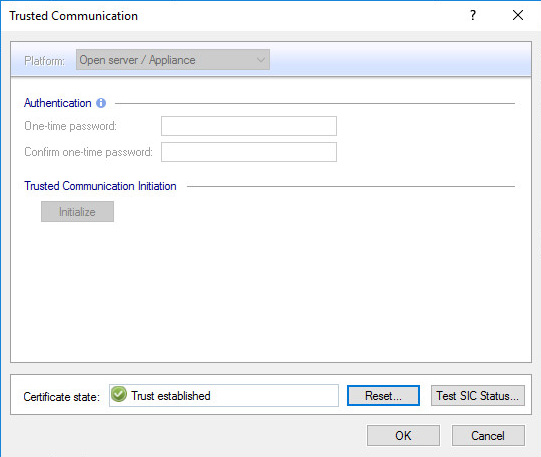
2.4 Secure Internal Communication (SIC)
2.4.1 SIC Overview
2.4.2 One-time password for initializing trust
2.4.3 SIC status
2.4.4 Internal Certificate Authority (ICA)
2.5 Deployment Options
2.5.1 Standalone Deployment
2.5.2 Distributed Deployment
2.5.3 Bridge Mode
3 Check Point Products
3.1 Security Gateways
3.2 Smart-1 Appliances
4 Installation and Initial Setup
4.1 Minimum System Requirements / Open Server Hardware Requirements
4.1.1 Security Management Server
4.1.2 Security Gateways
4.1.3 SmartConsole
4.1.4 Logging Requirements
4.2 Lab Topology
4.3 Demonstration: Security Management Server
4.3.1 Demonstration: Install Gaia for Security Management Server
4.3.2 Demonstration: Configure Gaia for Security Management Server
4.3.2.1 Demonstration: Gaia Login
4.3.2.2 Demonstration: IP addresses and MAC address
4.3.2.3 Demonstration: Default Gateway / Static Route
4.3.2.4 Demonstration: Hosts and DNS
4.3.2.5 Demonstration: Logout
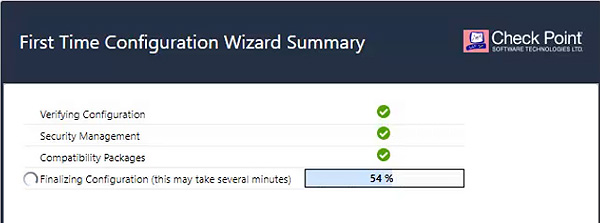
4.3.3 Demonstration: Install Security Management Server on Gaia / First Time Configuration Wizard
4.4 Demonstration: Security Gateway
4.4.1 Demonstration: Install Gaia for Security Gateway
4.4.2 Demonstration: Configure Gaia for Security Gateway
4.4.2.1 Demonstration: Gaia Login
4.4.2.2 Demonstration: IP addresses and MAC address
4.4.2.3 Demonstration: Default Gateway / Static Route
4.4.2.4 Demonstration: Logout
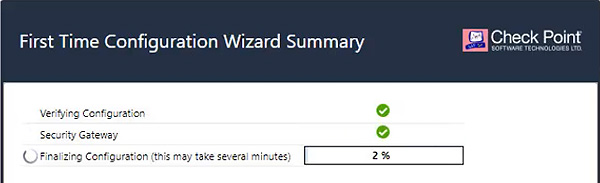
4.4.3 Demonstration: Install Security Gateway on Gaia
4.4.4 Demonstration: SmartConsole
4.4.4.1 Install SmartConsole
4.5 Demonstration: Accessing to security management server through SmartConsole
4.6 Demonstration: Establishing SIC between the Management Server and Security Gateway
5 Firewall Policy
5.1 Demonstration: View License Status
5.2 Administrator Collaboration and Sessions
5.2.1 Purpose of Sessions and Session Start
5.2.2 Publishing
5.2.3 Disconnect and Take Over
5.3 Anti-spoofing
5.3.1 Anti-spoofing Concepts
5.3.2 Demonstration: Network Topology and Anti-spoofing
5.4 Create Objects
5.4.1 Demonstration: Create Objects
5.5 Demonstration: Create Access Control Policy
5.6 Demonstration: Verify Access Control Policy
5.7 Demonstration: Install Policy
5.8 Stealth rule and Cleanup rule (Best Practices for all Rule Bases)
5.8.1 Demonstration: Stealth rule and Cleanup rule
5.9 Implied Rules
5.9.1 Demonstration: Implied Rule
5.10 Policy management and version control
5.10.1 Policy Package Management and layers
5.10.1.1 Demonstration: View Existing Policy Package (Standard)
5.10.1.2 Demonstration: Create a New Policy Package and then policy install to the Security Gateway
5.10.1.3 Demonstration: Rollback to Default Policy Package (Standard)
5.10.1.4 Demonstration: Delete a Policy Package
5.10.2 Database Revision
5.10.2.1 Demonstration: Display Database Revisions
5.10.2.2 Demonstration: View Database Revisions’ Content
5.10.2.3 Purge Database Revisions
5.10.3 Policy Installation History
5.10.3.1 Demonstration: View Policy Installation History
5.10.3.2 Demonstration: Revert to specific history
5.11 More about Rules: Section, Disable, Negate, Hit Count
5.11.1 Demonstration: Section
5.11.2 Demonstration: Disabling a Rule
5.11.3 Demonstration: Negate
5.11.4 Demonstration: Hit Count
6 Logging and Monitoring
6.1 Preparation of this chapter
6.1.1 Demonstration: Confirming / Enabling Logging on the Security Management Server
6.1.2 Demonstration: Confirming / Enabling Logging and Monitoring on the Security Gateway
6.1.3 Demonstration: Enabling SmartEvent on the Security Management Server
6.2 Logging
6.2.1 Rules Tracking Options
6.2.2 Demonstration: View Logs with filtering
6.2.3 Demonstration: Rule Logs
6.3 Event Analysis and Reports
6.3.1 Events
6.3.2 From logs to events
6.3.3 Views and Reports
6.3.3.1 Demonstration: Views
6.3.3.2 Demonstration: Reports
6.4 Monitoring Traffic, Connections and Check Point Products status
6.4.1 SmartView Monitor
6.4.2 Defining Status Fetch Frequency
6.4.2.1 Demonstration: Open SmartView Monitoring
6.4.3 Suspicious Activity Rules (SAM)
6.4.3.1 Demonstration: Suspicious Activity Rules (SAM)
6.4.4 Demonstration: Real-time monitor Security Gateway Traffic
6.5 Demonstration: System Alerts and Thresholds (e.g. CPU usage, free disk space, etc.)
6.6 Demonstration: Audit Logs
6.7 Export logs to a Excel file
6.8 Demonstration: “ping” by “Logs & Monitor”
7 Network Address Translation (NAT)
7.1 Preparation of this chapter
7.2 Basic Concepts
7.3 Hide NAT
7.3.1 Overview of Hide NAT
7.3.2 Demonstration: Hide NAT
7.4 Static NAT
7.4.1 Overview of Static NAT
7.4.2 Demonstration: Static NAT
7.5 Automatic and Manual NAT Rules
7.5.1 Automatic NAT
7.5.2 Manual NAT
7.5.2.1 Overview of Manual NAT
7.5.2.2 Demonstration: Manual NAT
8 Threat Prevention
8.1 Preparation of this chapter
8.2 Overview of Threat Prevention
8.2.1 Threat Prevention Components
8.2.1.1 IPS
8.2.1.2 Anti-Bot
8.2.1.3 Anti-Virus
8.2.1.4 SandBlast
8.3 Elements of IPS protection
8.4 Demonstration: Enable Threat Prevention (IPS) in the Security Gateway
8.5 Profile
8.5.1 Overview of Profile
8.6 Demonstration: Create an IPS profile and attach it in the policy.
8.7 Demonstration: Block “Large Ping”
8.8 Demonstration: TTL Masking
8.9 Demonstration: HTTP Headers Pattern
8.10 IPS under heavy loading
8.11 Geo Policy
8.11.1 Overview of Geo Policy and Updatable Objects
8.11.2 Demonstration: Updatable Objects
8.11.3 Demonstration: Geo Policy
8.12 Demonstration: Final tasks
9 Application Control and URL Filtering
9.1 Preparation of this chapter
9.2 Demonstration: Enable Application Control and URL Filtering + adjust Policy Layer
9.3 Application Wiki
9.4 Demonstration: Blocking YouTube
9.5 Demonstration: Monitoring Facebook
9.6 Demonstration: Block “Social Networking” websites / Block website based on categories
9.7 Deep packet inspection
9.8 Demonstration: Block traffic by HTTP Methods
10 Identity and Access Management
10.1 Preparation of this chapter
10.2 Managing Administrator Accounts
10.2.1 Permission Profiles
10.2.1.1 Overview of Permission Profiles
10.2.1.2 Default Permission Profiles
10.2.1.3 Demonstration: Create a Custom Permission Profile
10.2.2 Demonstration: Create an Administrator with Custom Permission Profiles
10.3 Authentication
10.3.1 User Authentication
10.3.1.1 Overview of User Authentication
10.3.1.2 Demonstration: Part 1 of 2 - Create a User for User Authentication
10.3.1.3 Demonstration: Part 2 of 2 – Configure User Authentication
10.3.2 Client Authentication
10.3.2.1 Overview of Client Authentication
10.3.2.2 Demonstration: Client Authentication (Manual sign on by HTTP)
10.3.2.3 Demonstration: Client Authentication (Manual sign on by Telnet)
10.4 Introduction to Identity Awareness
10.4.1 Identity Sources with AD Query
10.4.1.1 Overview of Identity Sources with AD Query
10.4.1.2 Process of AD Query
10.4.1.3 Limitations of Identity Sources with AD Query
10.4.1.4 Demonstration: Identity Sources with AD Query
10.4.1.4.1 Demonstration: Identity Sources with AD Query (Check AD DS) [Optional]
10.4.1.4.2 Demonstration: Identity Sources with AD Query (Enable Identity Awareness with AD Query)
10.4.2 Browser-Based Authentication
10.4.2.1 Overview of Browser-Based Authentication
10.4.2.2 Demonstration: Browser-Based Authentication for Internal Users
10.4.2.3 Demonstration: Browser-Based Authentication for Guests
11 Virtual Private Network (VPN)
11.1 Overview of Virtual Private Network (VPN)
11.2 Encryption
11.3 Hashing
11.4 Internet Key Exchange (IKE)
11.4.1.1 IKE phase 1
11.4.1.2 IKE phase 2
11.5 VPN Communities
11.6 VPN Topologies
11.6.1 Meshed VPN Community
11.6.2 Star VPN Community
11.7 Demonstration: Site-to-Site VPN
11.7.1 Demonstration: Site-to-Site VPN (Part 1: Preparation)
11.7.1.1 Demonstration: Preparation in HQ’s Security Gateway
11.7.1.2 Demonstration: Install Gaia in Branch’s Security Gateway
11.7.1.3 Demonstration: Install Security Gateway in Branch
11.7.1.4 Demonstration: Establish SIC between the Management Server and Branch’s Security Gateway
11.7.2 Demonstration: Site-to-Site VPN (Part 2: Build VPN)
11.7.2.1 Demonstration: Create objects representing sites’ networks and enable VPN feature in Security Gateways
11.7.2.2 Demonstration: VPN Community and Access Rule Configurations
11.7.3 Demonstration: Site-to-Site VPN (Part 3: Monitor VPN)
12 Miscellaneous topics
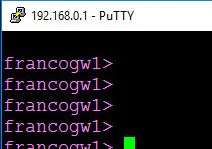
12.1 Command Line Interface (CLI), Standard Mode and Expert Mode
12.1.1 Command Line Interface (CLI)
12.1.1.1 Default Settings
12.1.1.2 Demonstration: Command Line Interface (CLI)
12.1.2 Standard Mode and Expert Mode
12.1.2.1 Standard Mode
12.1.2.2 Expert Mode
12.1.2.3 Demonstration: Expert Mode (with initializing expert mode password)
12.2 Web Services APIs
12.2.1 Demonstration: Enable the API server
12.2.2 Demonstration: Connect to the API Server and get the access token
12.2.3 Demonstration: Use API to create a host object (192.168.0.150)
12.3 Network Traffic Capturing (Wireshark)
12.3.1 Introduction to FW Monitor
12.3.2 FW Monitor vs tcpdump / snoop
12.3.3 Inspection points
12.3.4 Demonstration: Capture “ALL” traffic
12.3.5 More examples of Capturing
12.3.5.1 Host-specific capture
12.3.5.2 Port-specific capture
12.3.5.3 Host-Port-specific capture
12.3.5.4 Protocol-specific capture
12.4 Maintenance
12.4.1 License Management
12.4.2 Snapshot
12.4.2.1 Snapshot Content
12.4.2.2 Snapshot’s Best Practices
12.4.2.3 Create a snapshot
12.4.3 System Configuration Backup / System Backup
12.4.3.1 System Configuration Backup Content
12.4.3.2 Perform System Configuration Backup
12.4.3.3 Schedule Perform System Configuration Backup
12.4.3.4 Restore from System Configuration Backup
12.5 Infinity Threat Prevention system
12.5.1 Infinity Threat Prevention Profiles
12.5.2 Deployment Dashboard
12.6 Network Security for IoT Devices
12.7 Group objects
12.8 Security Zones
12.10 Web SmartConsole
13 Setup Home Lab
13.1 Prerequisites
13.2 Install VMware WorkStation Player
13.3 Topology
13.4 Management Server
13.5 Windows Server (PC)
13.5.1 Install Windows Server
13.5.2 Install VMware Tools
13.6 Ubuntu (Internet)
13.7 Ubuntu (Branch)
13.8 Security Gateway (HQ)
13.9 Security Gateway (Branch)
14 Additional Reading
14.1 Reset SIC (Security Internal Communication)
14.1.1 Background information
14.1.2 Demonstration: Reset SIC (Security Internal Communication)
14.1.2.1 Reset SIC: Part 1 (from management servers)
14.1.2.2 Reset SIC: Part 2 (from security gateways)
14.1.2.3 Reset SIC: Part 3 (re-establish SIC between security management server and security gateway)
14.2 “Trick” to reset Check Point administrators’ passwords
14.2.1 Demonstration: “Trick” to reset Check Point administrators’ passwords
14.2.2 Emergendisk
14.3 Connection persistence when installing a new policy
14.3.1 Keep all connections
14.3.2 Keep data connections
14.3.3 Rematch connections
14.4 LDAP (Lightweight Directory Access Protocol)
14.4.1 Introduction to LDAP (Lightweight Directory Access Protocol)
14.4.2 Retrieving information from a LDAP Server
14.4.3 Demonstration: LDAP Authentication
14.4.3.1 Demonstration: Enable User Directory
14.4.3.2 Demonstration: Create a host object to represent LDAP server
14.4.3.3 Demonstration: Create a LDAP Account Unit
14.4.3.4 Browse LDAP objects from Check Point
14.4.3.5 Demonstration: Create a LDAP Group
14.4.3.6 Demonstration: Create a rule to “use LDAP”
14.4.3.7 Demonstration: Verification
14.5 Check Point Cluster / HA (High Availability) solutions
14.5.1 Management High Availability (Management HA) for management servers
14.5.1.1 Introduction to Management High Availability (Management HA)
14.5.1.2 Demonstration: Install Gaia + Secondary Management Server
14.5.1.3 Demonstration: Add Secondary Management Server in SmartConsole
14.5.1.4 Demonstration: Verify the Management HA status
14.5.1.5 Demonstration: Failover between primary and secondary server
14.5.1.6 Synchronization Status and Trapshooting
14.5.1.6.1 When connecting to “Active”
14.5.1.6.2 When connecting to “Standby”
14.5.1.6.3 Troubleshooting Management HA
14.5.1.6.3.1 Not communicating
14.5.1.6.3.2 Collision or HA Conflict
14.5.1.6.3.3 Sync Error
14.5.2 ClusterXL for security gateways
14.5.2.1 Introduction to ClusterXL
14.5.2.1.1 ClusterXL High Availability
14.5.2.1.2 ClusterXL Load Sharing
14.5.2.2 State Synchronization, Cluster Control Protocol (CCP), Synchronization Network and Non-Synchronized Services
14.5.2.2.1 State Synchronization and Cluster Control Protocol (CCP)
14.5.2.2.2 Synchronization Network
14.5.2.2.3 Non-Synchronized Services
14.5.2.2.4 Momentum to considering services not to be synchronized
14.5.2.3 ClusterXL Load Sharing Modes
14.5.2.3.1 Introduction to ClusterXL Load Sharing Modes
14.5.2.3.2 High Availability (ClusterXL)
14.5.2.3.3 Load Sharing
14.5.2.3.4 Active-Active
14.5.2.4 Demonstration: Install Gaia + Security Gateway with ClusterXL capability
14.5.2.5 Demonstration: Steps to create a cluster
14.5.2.6 Demonstration: Verify ClusterXL status
14.5.2.7 Miscellaneous topics in ClusterXL
14.5.2.7.1 Sticky connections and non-sticky connections
14.5.2.7.1.1 TCP 3-Way handshake of non-sticky connections
14.5.2.7.1.2 Sticky Decision Function
14.6 Enable cluster membership for this gateway
14.7 QoS
14.7.1 Introduction to QoS
14.7.2 Steps of configuring QoS
14.7.2.1 In SmartConsole
14.7.2.2 In SmartDashboard
14.7.3 Demonstration: QoS
14.7.3.1 Demonstration: Preparation
14.7.3.2 Demonstration: Enable QoS in Security Gateway
14.7.3.3 Demonstration: Configure Policy Layer for QoS
14.7.3.4 Demonstration: Configure a QoS rule
14.7.4 More about Check Point QoS
14.7.4.1 Bandwidth allocation and rules
14.7.4.1.1 Weight
14.7.4.1.2 Guarantees
14.7.4.1.3 Limit
14.7.4.2 Action types
14.7.4.2.1 Simple
14.7.4.2.2 Advanced
14.7.4.3 Sub-rules
14.7.4.4 Examples of rule design
14.7.4.4.1 Example 1: Weight
14.7.4.4.2 Example 2: Weight + Guarantee
14.7.4.4.3 Problematic QoS Rule 1
14.7.4.4.4 Problematic QoS Rule 2
14.7.4.4.5 Problematic QoS Rule 3
14.7.4.4.6 Problematic QoS Rule 4
14.8 More about clish and mgmt_cli
14.9 CoreXL / Dynamic Dispatcher and SecureXL
14.9.1 CoreXL / Dynamic Dispatcher
14.9.2 SecureXL
14.10 Default users and roles in Gaia.
14.11 Introduction to Mobile Access
14.12 Smart Event Automatic Reactions
14.13 CPUSE (Check Point Update Service Engine)
14.14 Check Point ThreatCloud
14.15 VRRP (Virtual Router Redundancy Protocol)
 付款。
付款。